Introducing MAX — Take supply chain cyber risk management to the MAX
For Insureds: Understand claim drivers, enhance cybersecurity to lower your cyber insurance costs
Leverage AI-powered predictive data and analytics can help you protect your business while lowering the cost of cyber insurance

Increase security program ROI by reducing your exposure & cyber insurance costs
Cyber insurance requirements are driving the adoption of cybersecurity best practices across all industries. Adherence to these requirements can improve the ROI of security programs since they often determine whether or not your organization can obtain cyber insurance at favorable pricing and coverage terms. SecurityScorecard enables insurance buyers to strengthen security programs, demonstrate their cybersecurity capabilities, and get rewarded by insurers for lower rates for implementing cybersecurity best practices.
A View Inside
Increase insurability with key security controls

Create Business Value Through Security
- Reduce the impact of security incidents: Ensure your organization can obtain sufficient cyber insurance coverage to recover the losses from insurable incidents.
- Drive down operational expenses: Lower the costs related to procuring cyber insurance including resourcing required to achieve underwriting requirements and the annual policy premiums.
Critical Capabilities

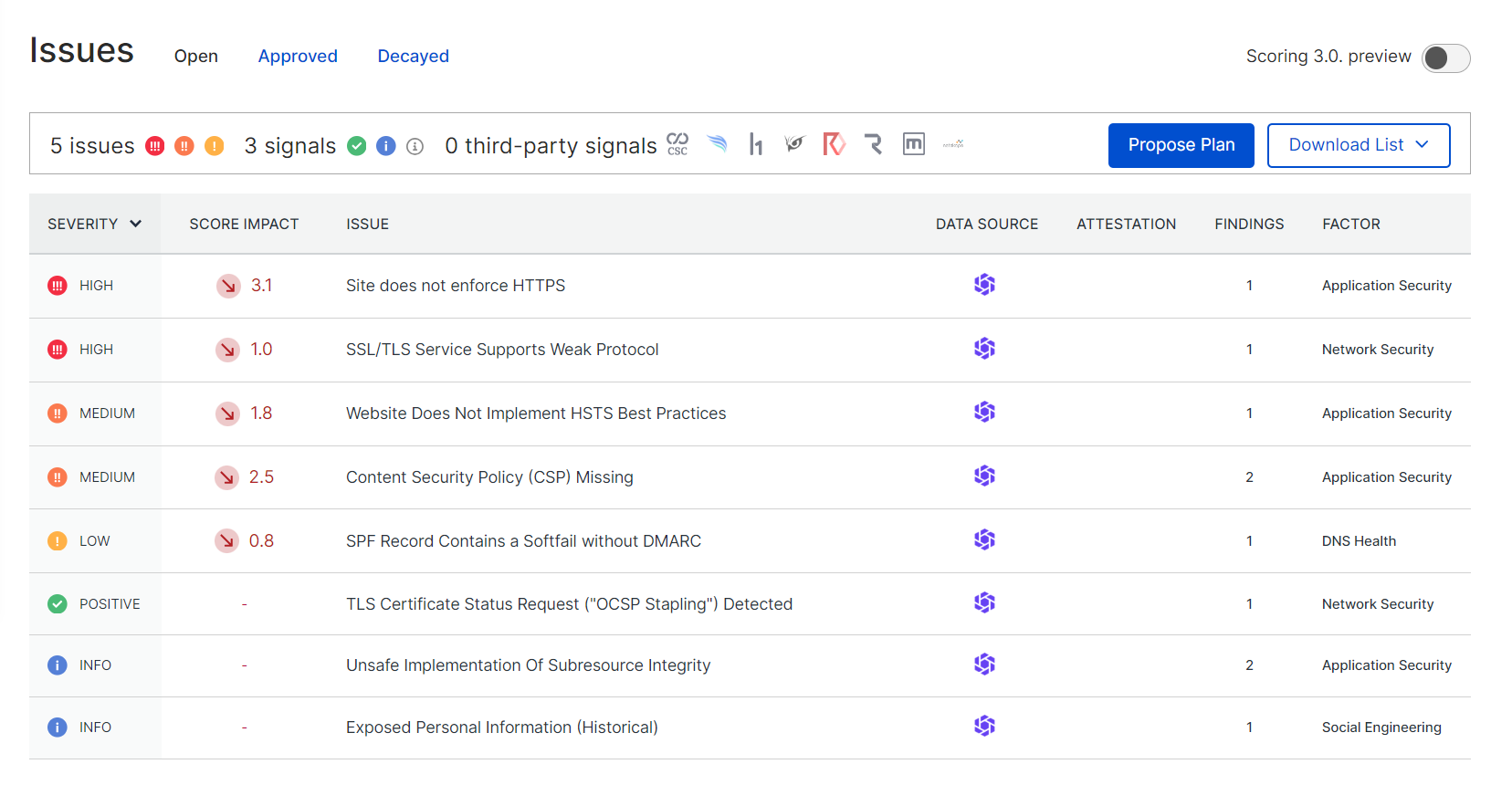
Continuous risk identification & monitoring
AI-powered analytics alerts you to new issues that could impact a successful insurance renewal

Use Score Planner to improve your rating
Leverage the power of AI to quickly analyze the risk and create a plan to improve your cyber hygiene

Leverage the power of security ratings
An “A” rating indicates lower risk and may reduce your cyber insurance premium and increase coverage

Prove you cybersecurity posture
Insurers use SecurityScorecard to identify risk. Resolving findings may improve your insurability
Insurance Discounts
Get a quote for discounted cyber insurance from these insurers
Hear From Our Customers

“SecurityScorecard has allowed me and my team to automate and scale many of the functions of our vendor risk management program as well as continuously monitor their internal and third-party security posture.”
Virgin Pulse Chief Information Security Officer1 / 0
Explore More
There is much more to the SecurityScorecard platform.