How technology companies secure every surface
Safeguard your fast-growing hyperconnected business from supply chain cyber attacks. Eliminate vulnerabilities and protect your own attack surface.

Tech companies stay ahead of attackers with SecurityScorecard
With a massive amount of confidential consumer and business data, as well as having many products in their third-party ecosystem, tech companies are a prime target for hackers. Technology companies that leverage SecurityScorecard can gain instant insight and take action to minimize the risk of breach due to a vendor or business partners’ cyber weaknesses.
-
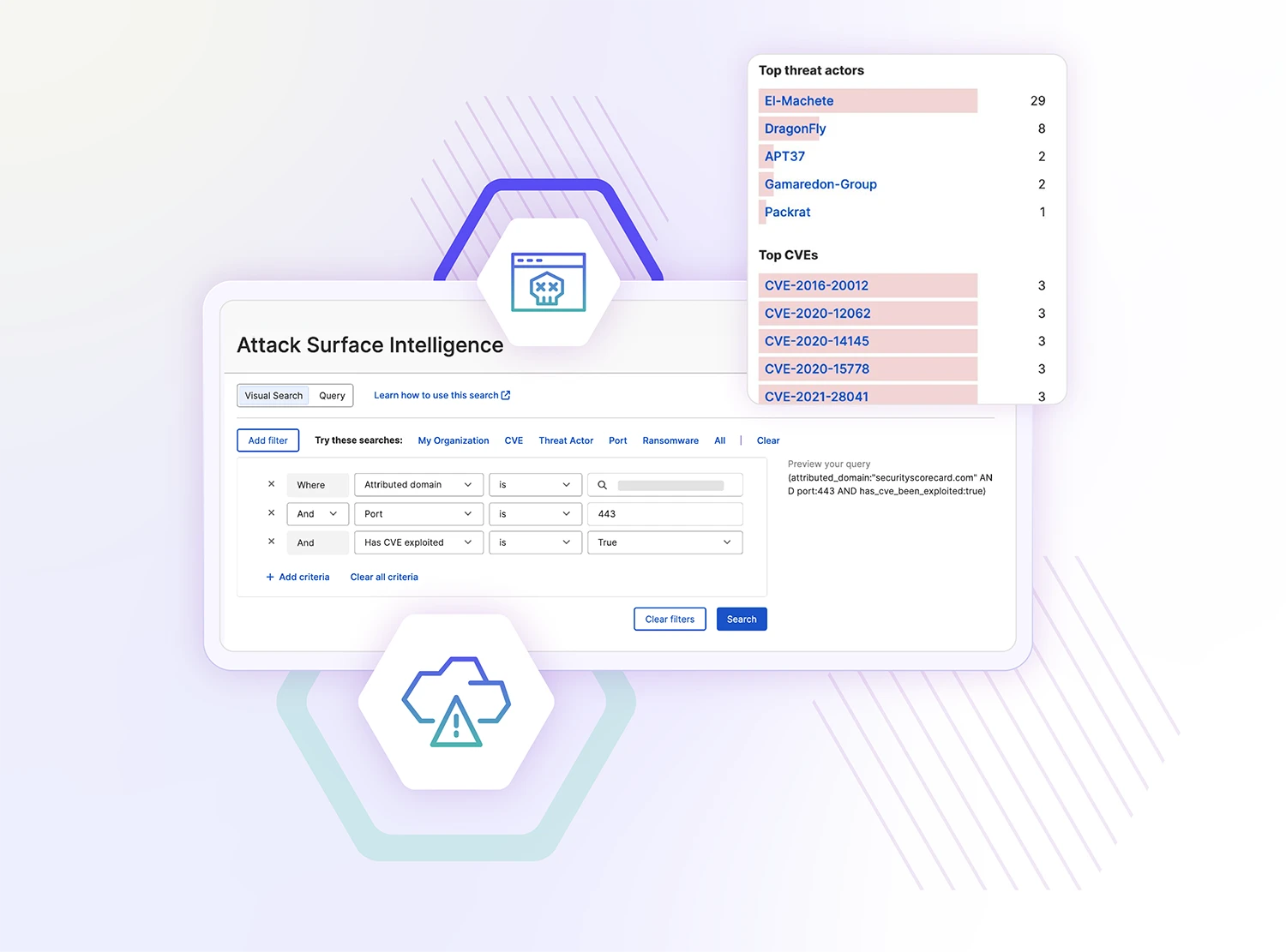
Protect your own attack surface
Understand how specific risk issues affect your security rating and prioritize mitigation to improve your cybersecurity posture. SecurityScorecard gives you access to tailored remediation plans so you can take the right steps to meet your goals.
-
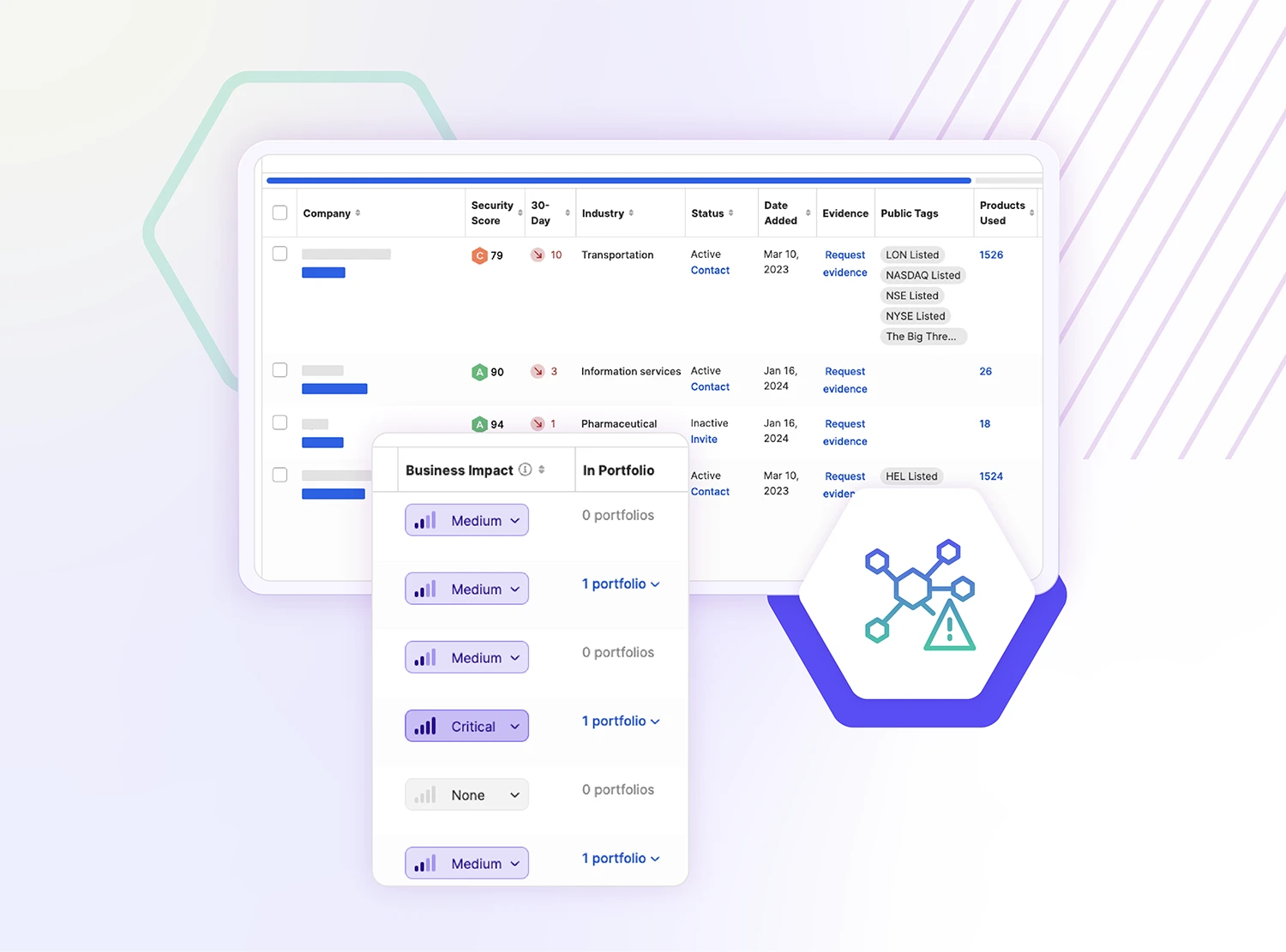
Identify threats in your third-party ecosystem
Your third parties can be your weakest link. SecurityScorecard is trusted by over 3,000 customers to identify and resolve cybersecurity issues across their supply chain.
-
See cyber risks across your extended supply chain
Know the unknown. Illuminate your third-parties’ supply chain to identify risks in your fourth-party ecosystem and beyond. Instantly visualize how you are connected to high-risk suppliers and discover vendors directly connected to you that were previously unknown.

Hear from our customers
-
“SecurityScorecard makes it possible to speed up our response when a problem is found and check that it has been remediated.”
Yuji Arai Executive Director, Information System Group, Network Value Components (NVC)View1 / 0
-
“Most of us do not know exactly when there is a breach, so our reaction time is very important. The platform allows us to find gaps and exposures quickly, and accurately. Before having this, we were wearing blinders.”
Director of Information Security Cloud-based Human Resource Solution providerView1 / 0
-
"SecurityScorecard offers us that kind of real-world view of a vendor’s security platform. What is the likelihood of them having a breach based on how secure (they are) and how well will they act on security across their estate?”
Matt Hodge Director of Technical Operations, ExclaimerView1 / 0