Daixin Team Ransomware Group Claimed Airline Ransomware Attack
Executive Summary
-
An information security researcher reported on November 20 that the Daixin Team ransomware group had claimed that a recent attack against an airline had resulted in a breach exposing the personal data of all airline employees and five million passengers.
-
Following this report, the SecurityScorecard Threat Research, Intelligence, Knowledge, and Engagement (STRIKE) Team consulted internal and external data sources to identify possible methods by which Daixin Team compromised the victim organization.
- STRIKE identified evidence suggesting two possible (and not mutually exclusive) paths by which the threat actors may have accessed airline systems:
-
Traffic data and files containing the victim domain suggest that attackers employed information-stealing malware in the early stages of the attack.
-
Other traffic and Attack Surface Intelligence (ASI) data revealed communication between a vulnerable airline IP address and IP addresses linked to malicious activity targeting vulnerable services.
-
-
These findings may indicate activity similar to that identified in previous ransomware investigations, suggesting a possible overlap in the tactics, techniques, and procedures (TTPs) of Daixin Team and the threat actors responsible for earlier incidents.
Background
An information security researcher reported on November 20 that the Daixin Team ransomware group had claimed that a recent attack against an airline had resulted in a breach exposing the personal data of all airline employees and five million passengers. This follows CISA’s October 21 publication of a #StopRansomware alert regarding the Daixin Team ransomware group.
The alert names spear phishing with malicious attachments as a Daixin Team reconnaissance technique, noting that the group has stolen credentials for later use by distributing malicious attachments in spear phishing emails to employees of target organizations. While researchers have not observed malicious documents that mention the airline, the HTML files discussed below may reflect a slight variation on this technique. The attacker might have sent spearphishing emails with links rather than attachments; these links could have similarly led to malicious downloads that facilitated credential theft; compromised credentials have also figured prominently in the group’s initial access techniques, with the group having previously leveraged exposed credentials to access target organizations’ servers.
Daixin has also exploited public-facing applications in the past by leveraging unpatched vulnerabilities in VPN servers for initial access and is known to move laterally across victim networks using both SSH and RDP hijacking. While STRIKE has not identified vulnerable VPN servers, SecurityScorecard’s ASI tool has identified a vulnerable, public-facing SSH server (discussed at greater length below) that the group may have targeted.
To identify the TTPs that Daixin Group may have employed in this attack, STRIKE leveraged traffic data provided by a strategic partner, which reflected roughly two months of communication involving IP addresses SecurityScorecard attributes to the victim organization and then enriched this data by consulting SecurityScorecard’s ratings platform, ASI tool, and internal threat intelligence platform and then enriching the data contained in those internal sources by cross-referencing it with data available in public cybersecurity information-sharing platform VirusTotal.
Findings: IP Addresses Communicating with This and Previous Ransomware Victims
STRIKE compared the traffic data involving the victim airline to data collected during previous ransomware investigations and found that 272 IP addresses observed in this most recent collection had also communicated with other ransomware victims. While this may, on its own, suggest that those 272 IP addresses may have been involved in the attack against the airline, of these IP addresses, other vendors have already linked eighty-three to malicious activity, indicating that they are especially likely to have been part of the compromise. Both groups of IP addresses are available in the appendices below.
Findings: Possible SSH Brute Force Attack
By pairing the traffic data they collected with VirusTotal and SecurityScorecard’s Attack Surface Intelligence (ASI) tool, STRIKE also observed evidence suggesting that the attackers may have targeted a vulnerable SSH service during the early stages of the attack. The traffic data contains 1,485 flows over port 22 (the default port for SSH) involving 332 unique, non-airline IP addresses. STRIKE then consulted both VirusTotal and ASI to further investigate those IP addresses and found that either VirusTotal community members or ASI linked the majority (289 of 332) of the non-airline IP addresses to SSH brute force attacks.
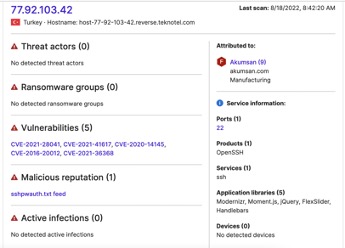
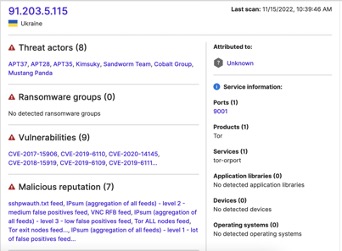
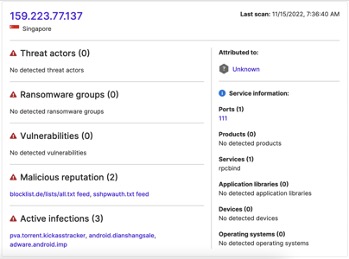
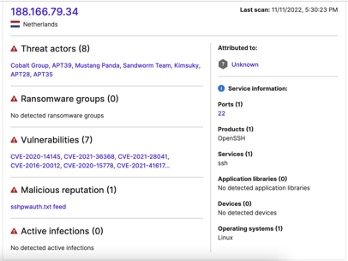
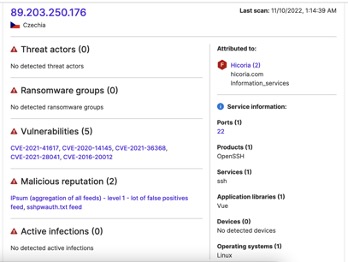
Images 1-5: ASI has linked many of the IP addresses communicating with airline assets to previous attacks against SSH services
Most of those flows (1,117 of 1,485) involved an airline IP address where ASI found port 22 open and running vulnerable SSH software. Given that repeated traffic in a relatively small amount of time is a common indication of a brute force attack, it may additionally bear noting that port 22 of this IP address experienced particularly heavy concentrations of traffic on (in descending order of flow count) November 3, September 24, November 6, September 25, and September 23.
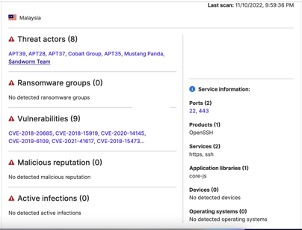
The recent advisory regarding Daixin Team does not name brute force attacks on SSH services as one of the group’s established TTPs, but does note that the group has compromised SSH services in the past. While it is thus possible that the traffic suggesting a brute force attack is unrelated to Daixin’s compromise of the airline, it may also reflect a more minor deviation from the group’s patterns when targeting those services. Moreover, STRIKE has observed evidence that groups responsible for recent ransomware attacks may have targeted similarly vulnerable SSH services. Other researchers observed earlier ransomware groups employing similar techniques in 2016 and 2019.
Findings: Additional Risky SSH Traffic
While investigating traffic over port 22, STRIKE researchers identified a series of large data transfers from port 22 of an external IP address, 209.97.172[.]51, to an airline-attributed IP address where SecurityScorecard’s ratings platform observed outdated browsers and OS.
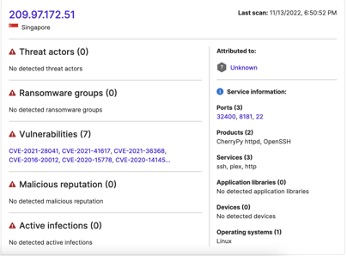
ASI shows that the media platform Plex is one of the services used at 209.97.172[.]51. While this may not relate directly to the ransomware incident, it could reflect deficiencies in the airline’s overall cybersecurity hygiene; the large transfers of data to an airline IP address from one where Plex is running could indicate that an airline employee was downloading entertainment media while connected to the company network.
While non-business application use does not in and of itself indicate compromise, it suggests broader cyber-hygiene issues: organizations’ acceptable use policies normally prohibit it, so this traffic may indicate insufficient adherence to, or enforcement of, that policy. Moreover, downloads of unofficial versions of media products can contain malware, so this traffic could represent a risk, depending upon the specific contents of the transfers it reflects. The observation of out-of-date software in use at the same airline-attributed IP address may compound these risks; malware sometimes distributed in unofficial media downloads often exploits the vulnerabilities software updates remedy, and if nothing else, it suggests further issues in the company’s cyber hygiene, as it may reflect insufficient adherence to, or enforcement of, a patching policy.
Findings: Redline Infostealer Traffic
69,996 of the 332,291 observed flows involved 1,042 IP addresses (available in an appendix below) that a strategic partner has linked to the Redline information-stealing malware, which suggests that attackers used Redline or other malware similar to it during the compromise. Analysts have observed initial access brokers using Redline to compromise credentials ransomware operators can later use it to access target systems and encrypt them. They have also observed Redline delivering ransomware as a second-stage payload. Communication between the victim network and Redline-linked IP addresses may therefore indicate that threat actors used Redline or another Trojan like it to steal airline credentials or deliver ransomware after initially infecting airline devices with a Trojan. Given that Daixin Team has reused compromised credentials to access victim systems in previous attacks, some of this traffic may reflect credential thefts that enabled subsequent stages of the attack.
Files recently submitted to VirusTotal may reflect similar activity: vendors have linked many files that contain the airline’s name or domain to various Trojans; this traffic, in combination with these files, may suggest that attackers employed an information-stealing Trojan like Redline in the early stages of the attack.
Findings: Recent VirusTotal Submissions Containing Airline Domain
In a two-month period around the time of the attack (September 21 to November 21), sixty-six files containing the victim organization’s domain, which vendors have linked to malicious activity, appeared on VirusTotal. Of these, vendors have linked fifty-four to various Trojans, and twelve are PDFs containing airline itineraries. The SHA-256 hashes of the files in each of these two groups are available in the appendices below.
Of the fifty-four files that appear malicious, slightly more than half (twenty-eight) are HTML files containing embedded JavaScript, which vendors detect as either generic Trojans or as the Wacatac, Cryxos, CoinMiner, or JS.Iframe Trojans. These files do not appear to have targeted the airline directly; most seem to be HTML for blogs or other websites with information for tourists, which link to the airline’s website when discussing the carriers serving the regions upon which they focus. However, two files’ contents suggest that they may have been more likely than others to attract the attention of airline personnel and may offer further evidence of credential theft leading up to the encryption of the target organization’s systems.
The files identified by the SHA-256 hashes A4870d0353d7f4beaaf25dc14a6c0577baf7ec3b68d02a76eacae4efca1514e3 and 539a23d4e9abb0bf486b1a080696c937b091a4c9c65669ec796087e2899dba2b appear to come from a website dedicated to share career and recruitment information about the airline industry and share a common detection, Trojan:Script/Wacatac.B!ml. Threat actors often use Wacatac to steal information (including credentials) from infected devices and distribute it by concealing it in downloads of unofficial versions of media products (possibly reflected in some of the traffic discussed above) or by using JavaScript injected into a vulnerable website to display messages leading to downloads of it. It is possible, then, that a malicious advertisement or alert showed when an airline employee visited a site about other careers in the industry, which led the employee to a download of an information-stealing Trojan like Wacatac, enabling the theft of employee credentials later used to access airline systems.
While less likely to have attracted the attention of airline employees, the nine files detected as Cryxos may also merit some attention, given similar files’ appearance in other SecurityScorecard investigations. Cryxos refers to a family of malicious JavaScript files that display fraudulent alerts to users when they visit web pages hosting those files. These files typically enable tech support scams, warning users that their computer has been infected by a virus and instructing them to call a threat actor-controlled telephone number. While attackers typically use the call as an opportunity to extract payment information from the victim, in some cases, they direct the victim to install software that gives the attackers remote access to their computer, which could, in turn, facilitate data theft or the deployment of ransomware. While these files appear to have originated from websites aimed at tourists rather than airline employees, they link to the airline’s website. An airline employee could still have come across them and ended up falling victim to a message directing them to call the telephone number displayed as the result of malicious JavaScript embedded into a website discussing their employer. The following SHA-256 hashes identify the files that vendors have linked to Cryxos:
-
536643341b59fdcda8a0dcc4b53aa9fae2007eb8a43f28d70a0002883e85c75a
-
1dcf99e980765e4f410d59a1ff0612485630109229107be9d0445ebf685f3aba
-
d1ccc79acf1708e59e8c90103a314e0c39c7ff6399b1206ecc6af626e5f9c28c
-
88eee66cec5f917033c328651ab9374dd952ea822d753658fedd6807ed26e85b
-
B19050beb5b2c3712f746761fa0da3a722cf136f3429b13b35b3e2ee84b81ebc
-
D6b1db14c863b7252b3f6be01b43966e3f59cbfed7ff96df5b84b46e112a6791
-
25319eeed6a5fb70decebb9699570205261d494df144c958965dd39e35a2de35
-
294be49c71aa1b93d94bdeec778a9c4e399b3cbbed2d1b4158834003c6de52ab
-
Dbebd9e2fb4ce17eeca4449116cefcef4ce23e136d149d2de591317f3963f2e5
Unlike the above files, the PDF itineraries do not appear to behave maliciously, but they do contain passengers’ identifying information and may therefore represent a risk; their availability on a public platform could constitute an unintentional exposure of information by the affected airline in the wake of the attack. Incident response professionals often upload files to VirusTotal for additional analysis, so given these files’ submission dates, which are close to those of reports of the attacks, airline IT personnel or other parties supporting their response may have uploaded them after identifying them while investigating the attack, either to assess whether their contents were malicious (and therefore involved in the attack) or because attackers may have attempted to exfiltrate them as part of a larger effort to steal data.
These now-public files may present the airline with additional risks. While they do not contain credentials or payment information, they do contain airline passengers’ names, which other threat actors could easily abuse. The details in these documents could, for example, lead to the creation of more believable lures for subsequent spear phishing attacks by threat actors either contacting the named passengers and impersonating the airline or impersonating the passengers when contacting the airline or by informing later extortion attempts–a threat actor could, for example, download them and then use them to claim responsibility for an additional airline breach only to circulate (or threaten to circulate) the files after accessing them at the public site in question. Although SecurityScorecard cannot yet assess the full impact of these particular findings, they may nonetheless represent dimensions of risk that the airline may not have previously considered.
Conclusion
This information was gathered and analyzed to briefly preview some of STRIKE’s capabilities. Therefore, it bears noting that this is not an exhaustive list of issues related to the airline’s overall cyber risk exposure. However, the data researchers have collected and analyzed thus far may offer new insights into the attack and Daixin Team’s operations.
Traffic data and files available in VirusTotal suggest airline devices suffered from infections with information-stealing malware in the months leading up to the breach claimed by the Daixin Team ransomware group. Given that the group is known to reuse compromised credentials when accessing victim systems, such infections may have led to credential theft that enabled subsequent stages of the attack. Analysts have additionally previously observed the group targeting public-facing services and compromising SSH servers in the past; traffic data, when paired with ASI findings indicating vulnerable and publicly-exposed SSH services running at an IP address attributed to the victim airline, may suggest that the attackers also exploited this vulnerable asset when compromising the target organization. While they may reflect a slight variation in the publicly available TTPs linked to Daixin Team, these findings may also indicate activity similar to that identified in previous ransomware investigations, suggesting a possible overlap between the TTPs of Daixin Team and those of the threat actors responsible for previous incidents.
Appendix: Vendor-Detected IP Addresses Communicating With This and Previous Ransomware Victims
|
|
|
Appendix: IP Addresses Communicating with Airline and Previous Ransomware Victim Assets
|
|
|
Appendix: IP Addresses Linked to Redline Infostealer
|
|
|
Appendix: Vendor-Detected Files Containing Airline Domain, September 21-November 21
- adbba3097d481578543b69c5a87d7124b3cb9f0320cb596657f750e5a528cec4
- 536643341b59fdcda8a0dcc4b53aa9fae2007eb8a43f28d70a0002883e85c75a
- 1dcf99e980765e4f410d59a1ff0612485630109229107be9d0445ebf685f3aba
- A4870d0353d7f4beaaf25dc14a6c0577baf7ec3b68d02a76eacae4efca1514e3
- 363ec5f48f4228a27fe9830ba0e409bb52b72e7811488b1844f3d4ae7a36eb30
- Ad878241408ebd3a04e8380ab24397d556fab14ea5a17e6b3d15b83714aed00d
- 2afd539a74934c6525540d48dfcf668c4b20b9a376084a6acf4ab624ee667a8f
- d1ccc79acf1708e59e8c90103a314e0c39c7ff6399b1206ecc6af626e5f9c28c
- Bf690a399e1cbc42cedef4893133300622f88fc6e1bd711fab2970eecb9c1559
- Ecf21446e637bb70564d2826f9778911f883429f3235ac67de145e76752dcea1
- F3f86772eafec3f06f266a31361cfe8c76129fdc6d7ccf1943984218fad9661c
- 9594f7c5b1834d2ab32b510bce24c63d08d5799645cecbe952c1aad50bcf8ab7
- 88eee66cec5f917033c328651ab9374dd952ea822d753658fedd6807ed26e85b
- B240cac40e1e35306e3127735e5efe36b49ff16236e5ff31e6f8f66d0270bea4
- 4ba1c4407bf08ccecb276a155f8197c95ec523af3dbc86cd77df06bc326b4e57
- 2d1ea09628fdbdbf635f985c60a2794ec6cd52ba8657cd0ba278bcd61fecb36c
- B19050beb5b2c3712f746761fa0da3a722cf136f3429b13b35b3e2ee84b81ebc
- 539a23d4e9abb0bf486b1a080696c937b091a4c9c65669ec796087e2899dba2b
- 241a7c1152d90b27803b90d414d98ebc65a5bc1e5202840fa7706f1acd8ba8f6
- D10afa9478d5a52468bdd1d678cc59deab5d6c3dce5147100cb1fe772c20a8f9
- D6b1db14c863b7252b3f6be01b43966e3f59cbfed7ff96df5b84b46e112a6791
- Dc72fd0fd4c09b35c9da89ea4452c9dce2bff851583ef61903f6a2cf81ba4dad
- 604914b977e2c5f309c07a09fd494c1fa322bdc85fc9f367fc6c5f9bf83a200e
- 25319eeed6a5fb70decebb9699570205261d494df144c958965dd39e35a2de35
- 21dcfbf4f37590c052e953c41ca87a5293c99c50e2457c35f44d778b1ce87856
- D89828cefbca12b5d7bff533a9b4c110ff6f623f8ef02716d16aae7f5c6b2554
- 1ce07589cbb88757ae753726ed096c74cd21da5414a58e2db92cfeb850f2934d
- 7f403a23274f7d64d19d457ceab85cfb16337412198f4b96dca0941ab3baba29
- 1aab38523224293c41f9ccb2b62ef9595a36e3ddf0d06bf0faabb3bf407ddfbe
- 7c67fdfb2b29dd96324230640fdca59fdb86ced92ae23f67e8312efc51a1c73e
- E2138f5da9f50d7031b51732a11c8d27aa47564a80618cb1e4c87d05afc8be7f
- 294be49c71aa1b93d94bdeec778a9c4e399b3cbbed2d1b4158834003c6de52ab
- 1fdb166ad6fa6343221b0912d888d800e72339ea48f31e62c9014322c61c3fc8
- Bb3c62e586a9d3cc96d09e4be7f7871138b3e63b7e85f2a7f8ddc8f1dd575049
- 9c11f6f52b295a29157df3c87e103427f0f2c991a8010704af29e90b6f738e8b
- 91694a125900e2893cb02a983ad7c5f4a094709c09ddc8f6bb077ae293d0928e
- Dbebd9e2fb4ce17eeca4449116cefcef4ce23e136d149d2de591317f3963f2e5
- F549e6ae7de422040c4c8d8016a3f385bb33fe92b688578f3e27b404cd1fb29d
- 3104e0c1c075356053f6cf560d3d5da6ebf54710c0bf0128301a4c7fa3a28a1b
- 1687d33e163f11256439ec46a08ebadf4cdd805b8ba4308dbf6d9cba8e2dc62c
- 009d841bc61b21e9770b6242799af0f47509fdac2a0d5e390cff245daf22defd
- Bd068ba67e12a2d5a558ff0741ab9807efa64ed973b86315199bab4ef173a797
- 7364908dcd95717fba9d8091ea52c38121a12c43d72c898da111367219ff50ce
- 4e8943bd98ea8b8576f86faaab4b4459ded96f0f9b9441d65934c87a09fc23cf
- Ce38c57e209181f24ef60e14f3414c2c78a170f9c5acf5156cd410891ca622f7
- 1d5052afa786bbd60dfc93ebcbbe764a7d1ab504c56529b35340618bc949cc0f
- A06512ba744c52bfe7dc6d94cb00b5ab7cbebe625953ed7699a3edcd74ae3304
- 2fa02bfb75350292163c68fc12bcb05e1fd485a8c1ef68a238935014384bdad7
- 84b14c8b9b61ea915fb2eee001e965fcc37d6cd2e677881e2e0db7fc958f1b44
- 756273e9525c93229234579baf1a6f707b09a9dd47a205de880333c1d2af6a2b
- 11ed0f8f42c14e86bf09c05497f527505a192b12c9378b1dbc810bc062292dee
- 14534fd49c25b8287a6cd4ea8c0947bc4b74986710100484d7ae872442b056fc
- Ca2c2f59ef4cde66eb596457b679797847b0fbf67f9874d330d85bc19dee1de3
- 4d58ec16911455c2f95fc1f7bedca1e0d32bef642c8711143f0ee48fc8591118
Appendix: SHA-256 Hashes of Publicly-Exposed PDF Itineraries
- 2da803ed4960495f987aa6ce51552d0fc0ee9d7d6fb01d932cb978d2220e7e0f
- 789ddc8cf2bb7075190df7c081504fcf6aa3964f9a10914371635820b32c2083
- 8fab6267676e929b3140eda2109687802eb95bce7f2daa13cc64f4131f00ac86
- Faf1037e8e01c9823f0adee3d2d4ba17433bff18a6e849749d0277c9414771a0
- 657c4c5da82eb7a827da71521b1d570f7e6c65a4c6569c7120bfdd9f0d0ab0a2
- a387ae07a9cbfe11b3bff333f378214e0b3e2546fdf485becf12723b9a14b815
- 440a4da69abc77e38c11d9b992a882df75e2bb944951ed22f5e578ad1a0dfc0e
- f2459b016f6d7159eb6cf5dd5e8d3b4317a501436516012111d2b7d93d82cb36
- 386130be32e341f48343b0efbca960d1068484460fd5197553c2ac79f0140f99
- 7504587a6b1a75660993d77cdd4d0e58ade78de11f83bd06aab63e3536e18105
- 8ee256e414b4ecd56363b6dff34cc0b42798d9e65854881b7c6ace91e93060a1
- 8d8e747f48d87d876ba17938e951b783d49301ad1eb22f75596a72f5927ca5a8




