Ransomware Attack Against U.S. Public Housing Authority Linked to Previous Attacks
-
February 24, 2025Massive Botnet Targets M365 with Stealthy Password Spraying Attacks
-
February 13, 2025Lazarus Group is Infecting Open-Source Code. Are You at Risk?
-
February 6, 2025Insurance Carriers Face Unprecedented Supply Chain Cyber Threats
-
January 29, 2025Operation Phantom Circuit: North Korea’s Global Data Exfiltration Campaign
-
January 21, 2025Security Assessment of the Top 100 U.S. Gov’t Contractors
Executive Summary
- On January 3, local media reported that a major U.S. city’s housing authority had suffered a ransomware attack.
- The LockBit ransomware group, which has made false claims in the past, took responsibility for the incident.
- As of this publication, the housing authority has announced a disruption, but has not elaborated on the nature of the event.
- Despite the LockBit group’s previous false claims, SecurityScorecard assesses with moderate confidence that the organization in question did in fact suffer a ransomware attack.
Background
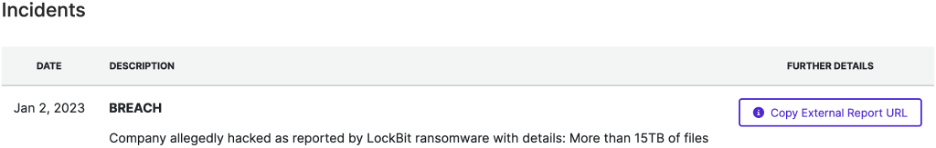
On January 2, the LockBit ransomware group added an entry for a major U.S. city’s housing authority to its data leak site, claiming to have exfiltrated 15 TB of data from its systems during the attack.
The affected organization has advised citizens that it is experiencing “technical difficulties” and warned of the possibility of resulting service disruptions, but has not acknowledged LockBit’s claims. While LockBit is a relatively long-standing ransomware group, it has recently made false claims regarding its attacks, which may, at first glance, call this recent claim into question.
Despite the group’s recent history of making questionable claims regarding its attacks, its affiliates remain willing and able to mount actual attacks, including a December incident that disrupted the operations of the Hospital for Sick Children (SickKids) in Toronto, Canada, for which the group apologized. Similarly, the SecurityScorecard Threat Research, Intelligence, Knowledge, and Engagement (STRIKE) Team’s investigation into the more recent housing authority attack suggests that it did in fact suffer a ransomware attack, despite the LockBit group’s previous false claims.
The group’s claim, moreover, comes alongside other evidence that ransomware groups have targeted housing authorities: on January 23, another local housing authority disclosed that a previously unconfirmed ransomware attack in September 2022 had exposed the personally identifiable information of over 200,000 people.
Findings
Following LockBit’s claim, STRIKE consulted internal and external data sources to identify evidence of a compromise affecting the housing authority. Data reflecting traffic to and from vulnerable IP addresses belonging to the affected organization indicates that they exchanged data with IP addresses previously observed conducting malicious activity. This data includes communication with IP addresses also observed communicating with previous ransomware victims and repeated and large data transfers that may reflect exfiltration by the attackers.
Researchers collected traffic data for eight IP addresses that SecurityScorecard’s ratings platform attributes to the housing authority; its Digital Footprint contains 319 IP addresses, so researchers limited their query to those addresses where SecurityScorecard also detected issues affecting the organization’s rating. Prioritizing those IP addresses where our ratings platform observes issues helped researchers focus their investigation upon the assets threat actors are more likely to target (attackers could begin their efforts by focusing on exploiting the observed issues and vulnerabilities). They additionally focused their query on a two-month period leading up to January 2 (the day LockBit published its claim on its leak site). This yielded 27,759 flows involving 607 IP addresses from outside the housing authority’s network.
Findings: Possible Exploitation of Known Vulnerability and Deployment of Remote Access Software
Two IP addresses other cybersecurity vendors have linked to malicious activity merit attention due to the frequency with which they communicated with a housing authority IP address. The first such IP address, 159.65.216[.]150, appeared in almost a fifth of all flows within the dataset. It and a single housing authority IP address exchanged data 5,904 times between November 2 and December 30. One vendor has linked this IP address to malicious activity. A domain linked to phishing and other malicious activity resolved to it as recently as December 30. Two malicious files communicate with it, and members of the VirusTotal community have linked it to exploitation of CVE-2022-30190, a Microsoft Support Diagnostic Tool (MSDT) vulnerability also known as Follina. Threat actors have leveraged Follina to distribute malware, including the Rozena backdoor, AsyncRAT (remote access trojan), and Qbot, which has previously delivered ransomware as a later-stage payload. SecurityScorecard’s ratings platform observed an outdated version of Windows running at the housing authority IP address involved in this traffic. It is possible that Follina still affected the version observed because a user had not yet applied the relevant update and attackers exploited it to drop information-stealing malware to the affected device, with the thousands of transfers observed reflecting the operation of that malware.
The second such IP address, 173.199.15[.]254, exchanged data with a single housing authority IP address 2,896 times between November 2 and January 2. SecurityScorecard has previously observed this IP address communicating with other ransomware victims. This communication likely reflects the remote access software attackers could have used to deploy ransomware.
Remote access software company LogMeIn, Inc. is the organization that operates 173.199.15[.]254. While the software has many legitimate uses, threat actors often induce their targets to install legitimate remote access software (TeamViewer is especially common) on their devices as a means of granting control of the device to the attacker, which can facilitate the deployment of ransomware. Traffic from a victim network to a LogMeIn-operated IP address may therefore reflect the attacker’s use of LogMeIn to control a victim device. In addition to vendors’ links to malware, members of the wider cybersecurity community have included 167.172.240[.]54 in collections referring to “remote IPs,” which may indicate that they have observed it attempting to access target systems remotely in other incidents, just as the STRIKE Team observed it communicating with previous ransomware victims.
Findings: Other Links to Previous Ransomware Attacks
Of the 607 IP addresses observed communicating with the housing authority in the sample period, 157 appeared in traffic samples the STRIKE Team collected from previous ransomware victims. This may suggest that those 157 IP addresses may have been involved in the attack, given that they also appeared in traffic collections from other ransomware victims. Moreover, of these IP addresses, other cybersecurity vendors have already linked twenty-eight to malicious activity, indicating that they are especially likely to have been part of the compromise. Both groups of IP addresses (those observed communicating with previous ransomware victims and those detected as malicious by other cybersecurity vendors) are available in the appendices below.
Additionally, a collection of related files that vendors have deemed malicious have communicated with forty of the IP addresses that also communicated with both the housing authority and previous ransomware victims. Communication between housing authority assets and these IP addresses may therefore reflect the use of malware within the housing authority’s network. The words “Ramnit” and “Hupigon” appear particularly frequently in the communicating files’ detections. Ramnit and Hupigon are both long-standing trojans that can facilitate data theft and the delivery of additional malware. Either could have been involved in the theft of credentials attackers later reused to access the housing authority’s system, but researchers have also observed Ramnit delivering ransomware as a second-stage payload, which communication with these IP addresses could also reflect. However, the traffic could also reflect the theft of credentials and other data or the delivery of a second-stage payload that enables the theft (rather than encryption) of victim data.
Findings: Possible Exfiltration
Of the 617 IP addresses with which the housing authority IP addresses communicated, other vendors have linked 114 to malicious activity. Of the traffic involving that more limited group, traffic to eighteen not previously discussed is likely to reflect exfiltration of housing authority data. This traffic involved large transfers of data most of these flows transferred 12.28 MB from a single housing authority IP address to these possibly malicious IP addresses. All vendor-detected IP addresses involved belong to either DigitalOcean or Rackspace (eighteen to DigitalOcean and one to Rackspace). Threat actors often abuse these hosting provider-owned IP addresses and members of the VirusTotal community have specifically linked one, 137.184.148[.]2, to ransomware–it has served downloads of a file that appears in a VirusTotal community graph titled “RU Ransomware Node Map.” Given their vendor detections and the size of the data transfers involved, traffic involving these IP addresses may suggest that this traffic reflects the exfiltration of data from the housing authority. However, it is also possible that large data transfers to and from provider assets could easily reflect more benign behavior like transfers to and from backups. Without internal visibility into the housing authority’s network, STRIKE cannot confirm if this was exfiltration, but the organization should have SIEM logs that describe these flows and can offer further insights. These IP addresses are also available in an appendix below.
Conclusion
While some commentators have noted a downward trend in the total number of ransomware attacks over the past year, the recent confirmation of a previous attack against another local housing authority suggests that local governments are still targets for ransomware groups, even if the overall number of successful attacks has been trending downward. Similarly, the available traffic data suggests that the housing authority in this more recent incident also suffered a ransomware attack. Not only did it communicate with the same IP addresses as previous ransomware victims in the months leading up to the attack, but the available traffic data also suggests a number of possible avenues by which an attacker like the LockBit group could have accessed their systems. Other researchers have linked one IP address that communicated regularly with a housing authority asset where SecurityScorecard observed an outdated (and possibly vulnerable) operating system in use to the exploitation of a vulnerability known to affect that operating system. Previous research has linked exploitation of this vulnerability to the distribution of malware that can facilitate data theft and the delivery of ransomware. Another IP address that frequently communicated with this same vulnerable IP address reflects the use of remote access software that attackers may have used against previous ransomware victims. Finally, a series of large data transfers leading up to the LockBit group’s addition of the organization to its data leak site may reflect theft of the data the group claims to have stolen. Based on this evidence, and despite the LockBit group’s previous false claims, SecurityScorecard assesses with moderate confidence that the organization in question did suffer a ransomware attack, which may in turn indicate that LockBit can pose a threat to both the private and public sectors even while researchers anticipate its demise.
Appendix: IP Addresses Communicating with Previous Ransomware Victims
- 186[.]237[.]182[.]227
- 103[.]170[.]83[.]200
- 89[.]203[.]251[.]217
- 103[.]92[.]28[.]58
- 103[.]131[.]95[.]88
- 154[.]68[.]199[.]18
- 104[.]131[.]0[.]131
- 146[.]20[.]132[.]166
- 192[.]241[.]157[.]60
- 159[.]203[.]152[.]67
- 157[.]245[.]70[.]89
- 146[.]20[.]128[.]141
- 146[.]20[.]128[.]74
- 146[.]20[.]128[.]192
- 159[.]89[.]246[.]130
- 146[.]20[.]128[.]197
- 146[.]20[.]132[.]69
- 23[.]253[.]41[.]115
- 146[.]20[.]128[.]108
- 146[.]20[.]132[.]67
- 146[.]20[.]128[.]46
- 146[.]20[.]128[.]82
- 157[.]230[.]89[.]169
- 146[.]20[.]132[.]139
- 206[.]81[.]3[.]80
- 146[.]20[.]128[.]164
- 162[.]13[.]161[.]130
- 82[.]202[.]70[.]139
- 159[.]65[.]196[.]12
- 178[.]128[.]135[.]232
- 143[.]198[.]114[.]225
- 157[.]230[.]85[.]253
- 69[.]20[.]43[.]192
- 165[.]227[.]204[.]179
- 23[.]253[.]31[.]170
- 167[.]99[.]116[.]82
- 157[.]230[.]54[.]161
- 134[.]213[.]193[.]62
- 157[.]245[.]241[.]7
- 146[.]20[.]128[.]178
- 159[.]65[.]235[.]198
- 146[.]20[.]132[.]153
- 206[.]189[.]180[.]223
- 64[.]185[.]181[.]238
- 192[.]33[.]214[.]47
- 137[.]184[.]201[.]253
- 192[.]33[.]96[.]102
- 195[.]176[.]26[.]206
- 134[.]213[.]70[.]247
- 137[.]184[.]71[.]88
- 159[.]203[.]145[.]121
- 192[.]241[.]241[.]96
- 146[.]20[.]128[.]147
- 145[.]40[.]89[.]200
- 45[.]232[.]73[.]54
- 146[.]20[.]128[.]155
- 45[.]90[.]111[.]243
- 146[.]20[.]132[.]70
- 146[.]20[.]132[.]205
- 146[.]20[.]128[.]107
- 146[.]20[.]132[.]71
- 146[.]20[.]132[.]72
- 146[.]20[.]128[.]75
- 131[.]108[.]156[.]1
- 45[.]175[.]101[.]66
- 146[.]20[.]128[.]169
- 192[.]241[.]145[.]39
- 103[.]28[.]156[.]170
- 143[.]244[.]220[.]80
- 185[.]14[.]184[.]154
- 146[.]20[.]32[.]58
- 35[.]212[.]200[.]165
- 146[.]20[.]128[.]175
- 161[.]47[.]17[.]28
- 38[.]43[.]193[.]211
- 157[.]245[.]81[.]154
- 173[.]233[.]161[.]109
- 38[.]43[.]199[.]234
- 162[.]209[.]40[.]62
- 146[.]20[.]132[.]132
- 146[.]190[.]223[.]184
- 142[.]93[.]9[.]247
- 45[.]55[.]58[.]103
- 168[.]167[.]72[.]179
- 146[.]20[.]132[.]78
- 72[.]3[.]137[.]178
- 104[.]131[.]48[.]134
- 193[.]5[.]60[.]8
- 146[.]20[.]128[.]47
- 146[.]20[.]128[.]83
- 146[.]20[.]132[.]39
- 184[.]106[.]10[.]77
- 146[.]20[.]128[.]66
- 146[.]20[.]128[.]151
- 159[.]203[.]41[.]221
- 63[.]131[.]135[.]115
- 67[.]192[.]28[.]17
- 159[.]89[.]188[.]11
- 72[.]32[.]131[.]23
- 159[.]65[.]221[.]212
- 167[.]71[.]87[.]161
- 146[.]190[.]219[.]246
- 184[.]106[.]60[.]185
- 159[.]223[.]167[.]67
- 23[.]160[.]192[.]118
- 206[.]189[.]180[.]179
- 147[.]182[.]218[.]51
- 137[.]184[.]135[.]187
- 67[.]205[.]128[.]102
- 146[.]190[.]219[.]244
- 198[.]199[.]86[.]237
- 161[.]35[.]102[.]197
- 50[.]57[.]31[.]206
- 130[.]60[.]204[.]10
- 159[.]223[.]138[.]235
- 103[.]110[.]98[.]174
- 173[.]199[.]15[.]254
- 146[.]20[.]132[.]179
- 167[.]172[.]231[.]60
- 178[.]128[.]55[.]198
- 35[.]212[.]198[.]217
- 146[.]20[.]128[.]138
- 146[.]20[.]128[.]144
- 146[.]20[.]128[.]87
- 159[.]203[.]123[.]152
- 146[.]20[.]132[.]161
- 159[.]89[.]102[.]253
- 98[.]129[.]164[.]22
- 35[.]210[.]239[.]72
- 146[.]20[.]128[.]162
- 35[.]214[.]223[.]115
- 50[.]57[.]205[.]124
- 173[.]203[.]158[.]113
- 174[.]143[.]40[.]29
- 146[.]20[.]132[.]154
- 138[.]197[.]225[.]96
- 134[.]209[.]118[.]223
- 35[.]210[.]214[.]151
- 89[.]203[.]250[.]36
- 146[.]190[.]72[.]74
- 35[.]214[.]236[.]176
- 146[.]20[.]132[.]192
- 72[.]32[.]100[.]43
- 173[.]203[.]164[.]184
- 146[.]20[.]128[.]153
- 63[.]131[.]135[.]96
- 50[.]56[.]23[.]157
- 35[.]212[.]212[.]222
- 35[.]212[.]217[.]28
- 35[.]212[.]211[.]70
- 35[.]212[.]133[.]238
- 146[.]20[.]161[.]1
- 72[.]32[.]236[.]222
- 184[.]106[.]54[.]1
- 173[.]203[.]187[.]1
- 162[.]209[.]117[.]196
- 162[.]13[.]192[.]130
Appendix: Vendor-Detected IP Addresses
- 89[.]203[.]251[.]217
- 45[.]232[.]73[.]54
- 38[.]43[.]193[.]211
- 178[.]128[.]55[.]198
- 206[.]189[.]130[.]158
- 206[.]189[.]139[.]206
- 198[.]199[.]93[.]44
- 157[.]245[.]81[.]154
- 107[.]170[.]246[.]28
- 178[.]62[.]64[.]242
- 192[.]241[.]206[.]53
- 157[.]245[.]240[.]224
- 192[.]241[.]145[.]39
- 204[.]48[.]16[.]71
- 192[.]241[.]197[.]125
- 173[.]233[.]161[.]109
- 45[.]232[.]73[.]57
- 192[.]241[.]196[.]158
- 168[.]167[.]72[.]179
- 162[.]243[.]139[.]19
- 104[.]236[.]128[.]11
- 159[.]203[.]240[.]10
- 107[.]170[.]235[.]15
- 167[.]99[.]7[.]23
- 168[.]167[.]72[.]97
- 192[.]241[.]210[.]182
- 139[.]59[.]181[.]152
- 137[.]184[.]60[.]119
- 198[.]199[.]116[.]78
- 137[.]184[.]149[.]253
- 134[.]209[.]118[.]223
- 104[.]131[.]0[.]222
- 103[.]131[.]95[.]88
- 103[.]239[.]252[.]66
- 198[.]199[.]119[.]170
- 139[.]59[.]165[.]170
- 24[.]199[.]92[.]95
- 137[.]184[.]58[.]169
- 104[.]236[.]128[.]18
- 68[.]183[.]239[.]110
- 167[.]99[.]87[.]194
- 159[.]223[.]167[.]67
- 103[.]92[.]28[.]58
- 167[.]99[.]115[.]182
- 161[.]35[.]205[.]87
- 206[.]189[.]229[.]81
- 45[.]55[.]45[.]210
- 64[.]227[.]24[.]23
- 45[.]232[.]73[.]35
- 162[.]243[.]131[.]5
- 192[.]241[.]202[.]200
- 157[.]230[.]226[.]26
- 142[.]93[.]9[.]247
- 128[.]199[.]92[.]153
- 64[.]225[.]124[.]42
- 192[.]241[.]197[.]61
- 134[.]209[.]97[.]150
- 146[.]190[.]76[.]162
- 146[.]20[.]132[.]132
- 139[.]59[.]12[.]104
- 198[.]148[.]92[.]176
- 143[.]198[.]208[.]71
- 137[.]184[.]148[.]2
- 159[.]223[.]112[.]213
- 165[.]22[.]177[.]53
- 167[.]172[.]145[.]161
- 134[.]209[.]212[.]251
- 68[.]183[.]24[.]222
- 144[.]126[.]232[.]151
- 138[.]68[.]107[.]18
- 89[.]203[.]250[.]36
- 170[.]233[.]117[.]110
- 206[.]189[.]180[.]223
- 116[.]90[.]227[.]242
- 68[.]183[.]88[.]253
- 174[.]138[.]79[.]19
- 167[.]172[.]73[.]5
- 146[.]190[.]219[.]152
- 154[.]68[.]199[.]18
- 45[.]55[.]64[.]46
- 143[.]244[.]202[.]121
- 102[.]220[.]15[.]219
- 102[.]220[.]15[.]104
- 200[.]50[.]249[.]222
- 104[.]248[.]6[.]235
- 191[.]37[.]28[.]117
- 173[.]203[.]187[.]1
- 72[.]32[.]131[.]23
- 157[.]245[.]241[.]7
- 134[.]209[.]120[.]236
- 137[.]184[.]201[.]253
- 159[.]203[.]94[.]125
- 134[.]209[.]172[.]238
- 157[.]245[.]97[.]223
- 178[.]128[.]135[.]232
- 104[.]131[.]100[.]255
- 146[.]20[.]132[.]192
- 45[.]58[.]138[.]186
- 146[.]190[.]248[.]226
- 131[.]108[.]156[.]1
- 165[.]22[.]176[.]62
- 38[.]43[.]199[.]234
- 206[.]189[.]180[.]179
- 167[.]71[.]91[.]220
- 159[.]65[.]49[.]110
- 104[.]236[.]116[.]147
- 165[.]232[.]182[.]249
- 102[.]220[.]13[.]85
- 131[.]108[.]156[.]113
- 192[.]241[.]212[.]178
- 173[.]199[.]15[.]254
- 159[.]65[.]216[.]150
- 196[.]10[.]52[.]57
- 165[.]232[.]104[.]83
Appendix: Vendor-Detected IP Addresses Involved in Large Data Transfers
- 134[.]209[.]118[.]223
- 64[.]227[.]24[.]23
- 157[.]230[.]226[.]26
- 128[.]199[.]92[.]153
- 137[.]184[.]148[.]2
- 159[.]223[.]112[.]213
- 165[.]22[.]177[.]53
- 144[.]126[.]232[.]151
- 206[.]189[.]180[.]223
- 146[.]190[.]219[.]152
- 143[.]244[.]202[.]121
- 173[.]203[.]187[.]1
- 157[.]245[.]241[.]7
- 134[.]209[.]120[.]236
- 137[.]184[.]201[.]253
- 146[.]190[.]248[.]226
- 206[.]189[.]180[.]179
- 159[.]65[.]216[.]150
- 165[.]232[.]104[.]83




