Executive Summary
- On March 14, Microsoft released a security update for a newly-identified vulnerability affecting all versions of Outlook for Windows.
- Current reports indicate that the vulnerability is under active exploitation by a threat actor group the cybersecurity community believes is acting on behalf of the GRU, Russia’s military intelligence agency.
- Shortly after the vulnerability’s publication, the SecurityScorecard Threat Research, Intelligence, Knowledge, and Engagement (STRIKE) Team began its investigation.
- Our Attack Surface Intelligence tool has revealed a population of servers that may be subject to this vulnerability. Our global network flow (NetFlow) analysis capability (available via professional services) has uncovered possible communication between target IP addresses and infrastructure involved in the exploitation of this vulnerability.
Background
On March 14, Microsoft released a security update for a newly-identified vulnerability affecting all versions of Outlook for Windows. The Computer Emergency Response Team for Ukraine (CERT-UA) first reported the vulnerability, now tracked as CVE-2023-23397, which can allow an attacker to escalate privileges by exposing authentication data and enabling its reuse in pass-the-hash (PtH) attacks. A subsequent report attributed the activity to the threat actor group tracked as APT28, STRONTIUM, Sednit, Sofacy, and Fancy Bear, which the cybersecurity community believes is acting on behalf of the GRU, Russia’s military intelligence agency.
Methodology
Researchers consulted SecurityScorecard’s Attack Surface Intelligence tool and leveraged its exclusive access to network flow (netflow) data to identify possible compromises resulting from the exploitation of the vulnerability. They first used Attack Surface Intelligence to identify possible target IP addresses and then collected a two-month sample of traffic involving those addresses.
Knowing that CERT-UA first identified the vulnerability, STRIKE Team researchers queried Attack Surface Intelligence for Ukrainian IP addresses where Outlook may be in use; this returned fifty-two results.

Image 1: Attack Surface Intelligence revealed a population of possibly affected servers in Ukraine.
Then, within these results, they sought to identify IP addresses used by organizations particularly likely to be the focus of nation-state activity, selecting two with hostnames suggesting that they belonged to particularly sensitive targets: a local government and a bank.
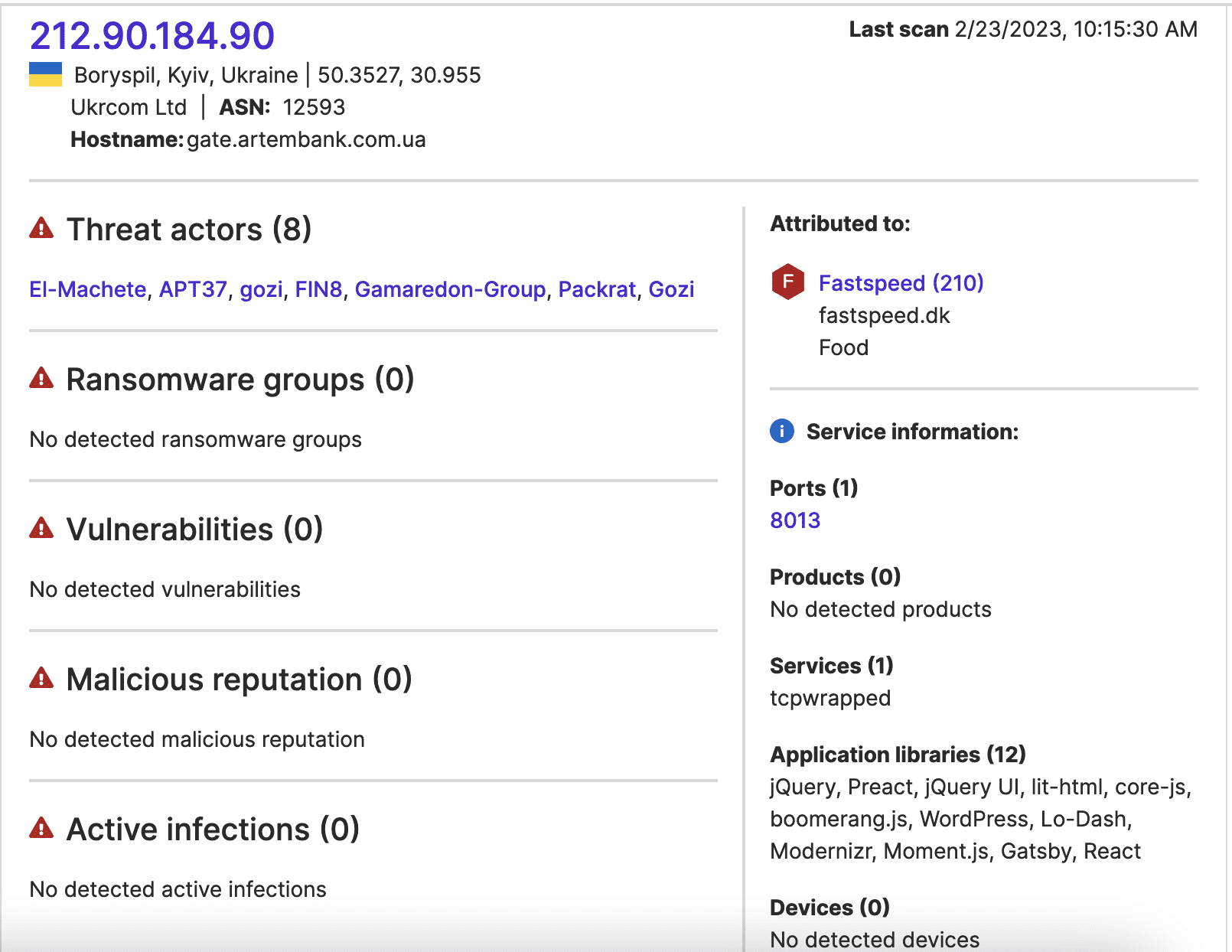

Images 2-3: Those IP addresses appearing to be used by a Ukrainian local government and bank may be of particular interest to nation-state threat actors.
Aside from the possibility of targeting based on their organizations’ sectors, Attack Surface Intelligence has connected both IP addresses to other threat actor groups, suggesting that they may suffer from vulnerabilities these groups may exploit. This may further suggest that they are more likely to suffer from other vulnerabilities exploited by other groups, like the newly-disclosed Outlook vulnerability.
In light of the possibility that these two IP addresses were particularly likely targets of the activity exploiting CVE-2023-23397, the STRIKE Team collected a sample of traffic to them, which resulted in a collection of 2,581 data transfers between January 15 and March 15. Within this sample, researchers sought further evidence of possible compromise.
Findings: NetFlow Analysis
Because the alert advises in favor of attention to port 445, researchers first queried the sample for traffic involving that port of the possible target IP addresses. The sample reflects suspicious traffic to both IP addresses at that port. Three IP addresses, two of which have vendor detections in VirusTotal, contacted port 445 of one possible target IP address on January 31, February 22, and 26. One of these same possibly malicious IP addresses and the other possible target IP address communicated on February 25.
Researchers next identified the largest data transfers within the traffic sample, as these may reflect exfiltration following an initial compromise. 268 transfers of 1 MB or more took place within the monitoring period; these involve fifty-six unique IP addresses. The vendors contributing to VirusTotal have already linked six to malicious activity. Fourteen others have appeared in traffic samples that STRIKE Team researchers collected during previous investigations. Of those within the sample, these IP addresses, therefore, may be particularly likely exfiltration targets, given their previous links to malicious activity.
These IP addresses appeared in investigations into incidents including ransomware attacks and other events likely to involve data theft claimed by, or attributed to, threat actors including the Black Basta, BlackCat, BlackMatter, Daixin, and LockBit ransomware groups.
The currently available research has linked exploitation of this particular vulnerability to a nation-state espionage group rather than a financially-motivated cybercriminal group, though, so the overlaps in these traffic samples may reflect multiple groups’ use of the same resources rather than indicating that ransomware groups have exploited the same zero-day vulnerability as an APT group.
Additionally, this traffic does not necessarily represent post-compromise exfiltration; the IP addresses involved belong to hosting and other IT services providers, so large data transfers to them could represent more benign behavior, like data backups. However, in light of the circumstances, it may merit closer attention from parties with internal visibility into the affected networks. Both groups of IP addresses are available in the appendices below.
Conclusion: Possible Mitigations
An update remedying the vulnerability is available for the affected versions of Outlook, so we advise that all Outlook for Windows users apply it. Microsoft has further recommended that organizations avoid using NTLM for authentication and block outgoing SMB (TCP port 445) traffic as additional mitigations.
APPENDIX: VENDOR-DETECTED IP ADDRESSES INVOLVED IN LARGE DATA TRANSFERS
- 162.243.189[.]2
- 104.248.80[.]227
- 46.101.219[.]91
- 134.122.92[.]140
- 165.22.64[.]123
- 82.196.7[.]246
APPENDIX: IP ADDRESSES APPEARING IN PREVIOUS SECURITYSCORECARD INVESTIGATIONS
- 178.62.222[.]113
- 146.20.128[.]172
- 178.62.203[.]207
- 167.71.9[.]19
- 146.20.128[.]202
- 142.93.53[.]200
- 143.244.220[.]80
- 69.20.43[.]192
- 161.35.176[.]170
- 165.227.78[.]137
- 165.22.7[.]208
- 188.166.0[.]147
- 143.244.196[.]143
- 83.217.98[.]225




