INTERNET INTELLIGENCE
Threat Intelligence Meets Risk Reduction
Are Hackers Out-Maneuvering Your Tools?
Exploitable Blind Spots Across Your Vendors
Hackers exploit non-standard ports and shadow IT that traditional scans miss. If you aren’t looking everywhere, they’re already inside.
Stale Data Wastes Time
Relying on monthly reports means making critical decisions based on stale data. By the time you see the risk, the breach has happened.
Security Noise is Killing Prioritization
The volume and complexity of modern threat intelligence overwhelms security teams, making it difficult to sift through the noise and accurately prioritize the most immediate and relevant threats.
Bridge TPRM and True Threat Intelligence
TITAN AI facilitates risk understanding for TPRM teams, and makes the data that a threat hunter needs for action readily available.
Trace C2 nodes and phishing domains back to their origin using deep-scan data and historical IP mapping. Don’t just look at today’s infrastructure, look back in time to identify hacker hiding spots.
Don’t rely on monthly snapshots. Reduce your window of exposure by getting 3,500+ ports re-verified every three days for a surgical, real-time view of risk.
Hackers try to bypass traditional scanners by hiding on arbitrary ports for example, running RDP on port 8443 instead of 3389). Gain visibility into these non-standard ports and services often missed by legacy scanners, including IoT and industrial protocols.
Global Intelligence to Secure Your Entire Ecosystem
The TITAN AI platform leverages the industry’s most comprehensive data lake to provide a 360-degree view of your attack surface. While others monitor only the essentials, we hunt for the hidden infrastructure and signals that define modern cyber risk.
- Port-Agnostic Visibility: Detect non-standard services, like SSH on port 443 or hidden databases.
- Persistent Adversary Tracking: Use JARM fingerprinting to identify malicious C2 servers by their behavior
- Shadow Asset Identification: Uncover the hardware behind generic proxies using advanced JA4TScan packet analysis.
- Gain visibility even when hackers try to bypass traditional scanners by hiding on arbitrary ports and services often missed by legacy scanners, including IoT and industrial protocols.
360°
view of your attack surface.

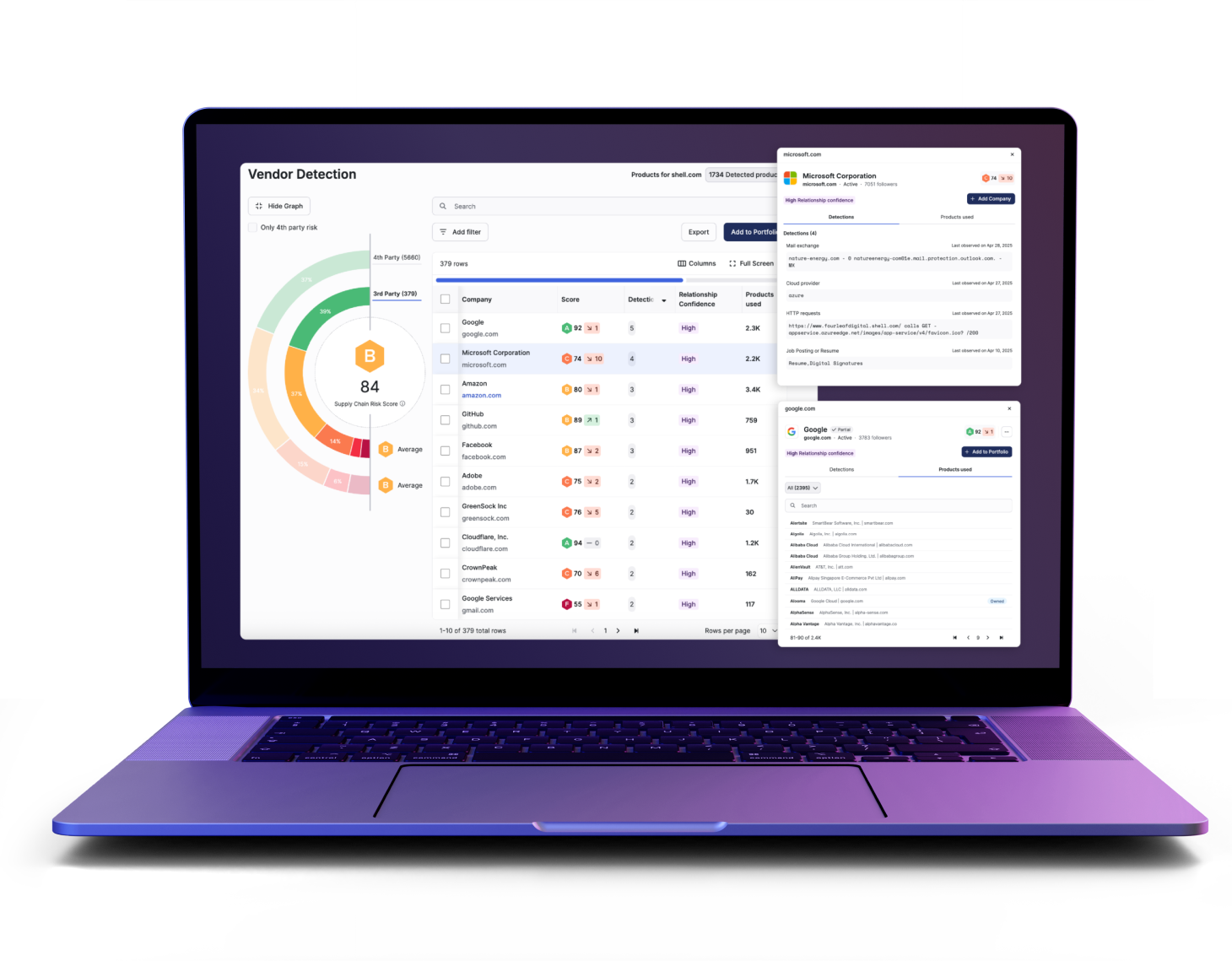
Meet The TITAN AI Platform
TITAN Watch
Foundational Visibility for Your Third Party Ecosystem
Gain a real-time, objective view of your posture and eliminate blind spots by discovering unseen third- and fourth-party connections.
TITAN Assess
Automate the Manual Security Assessment Grind
Prioritize what matters and eliminate manual toil through AI-powered questionnaire validation and automated risk tiering.
TITAN Secure
Operationalize Your Proactive and Continuous Third Party Defense
Operationalize threat response and proactively secure the cyber supply chain with built-in detection and collaborative remediation.
Related resources
Frequently Asked Questions (FAQs)
How often is the internet scanned?
We re-verify over 3,500 ports every three days to ensure the highest data fidelity available.
Can I integrate this data into my SIEM?
Yes, we offer robust APIs and pre-built integrations for Splunk, Sentinel, and other major SOAR/SIEM platforms.
Is this for my own posture or third-party risk?
The data can be used for both. Titan allows you to apply the same deep-scanning lens to any vendor or partner in your ecosystem.
Do you do JARM fingerprinting?
Yes, JARM fingerprinting can quickly verify server group TLS configurations, group disparate internet servers by configuration to identify providers like Google or Apple, and detect default applications, infrastructure, or malicious servers, including malware command and control.