Recently, a critical vulnerability tracked as CVE-2023-27997 was identified in Fortinet Fortigate appliances. Fortinet makes some of the most popular firewall and VPN devices on the market, which makes them an attractive target for threat actors. This vulnerability has been exploited by the Chinese APT group Volt Typhoon, among others, targeting governments and organizations worldwide.
As a result, Fortinet has released an urgent patch for affected systems. For a more detailed understanding of this vulnerability and the corresponding patch, you can read this Fortinet blog post.
Additionally, SecurityScorecard recommends the following steps for organizations to take to protect themselves from CVE-2023-27997:

- Update FortiOS devices to the latest version
- Close off access to any network management devices that may be exposed to the public internet, as encouraged by CISA in a recently released directive
Identify vulnerable Fortinet devices within your organization
SecurityScorecard’s Attack Surface Intelligence platform is able to identify any Fortinet Fortigate devices within an organization that may be exposed to the public Internet. Please note: The results from Attack Surface Intelligence are part of our ongoing data collection efforts and do not necessarily indicate that the devices are vulnerable, exploited, or unpatched. Continue reading for information on how to test whether a Fortigate device is vulnerable to CVE-2023-27997. SecurityScorecard is working diligently to ensure that IP addresses vulnerable to CVE-2023-27997 are tagged accordingly in SecurityScorecard and the Attack Surface Intelligence platform. In the meantime, we hope these resources help your organization identify, mitigate, and remediate any potential threats while staying ahead of the curve.Surface exposed Fortigate devices with Attack Surface Intelligence
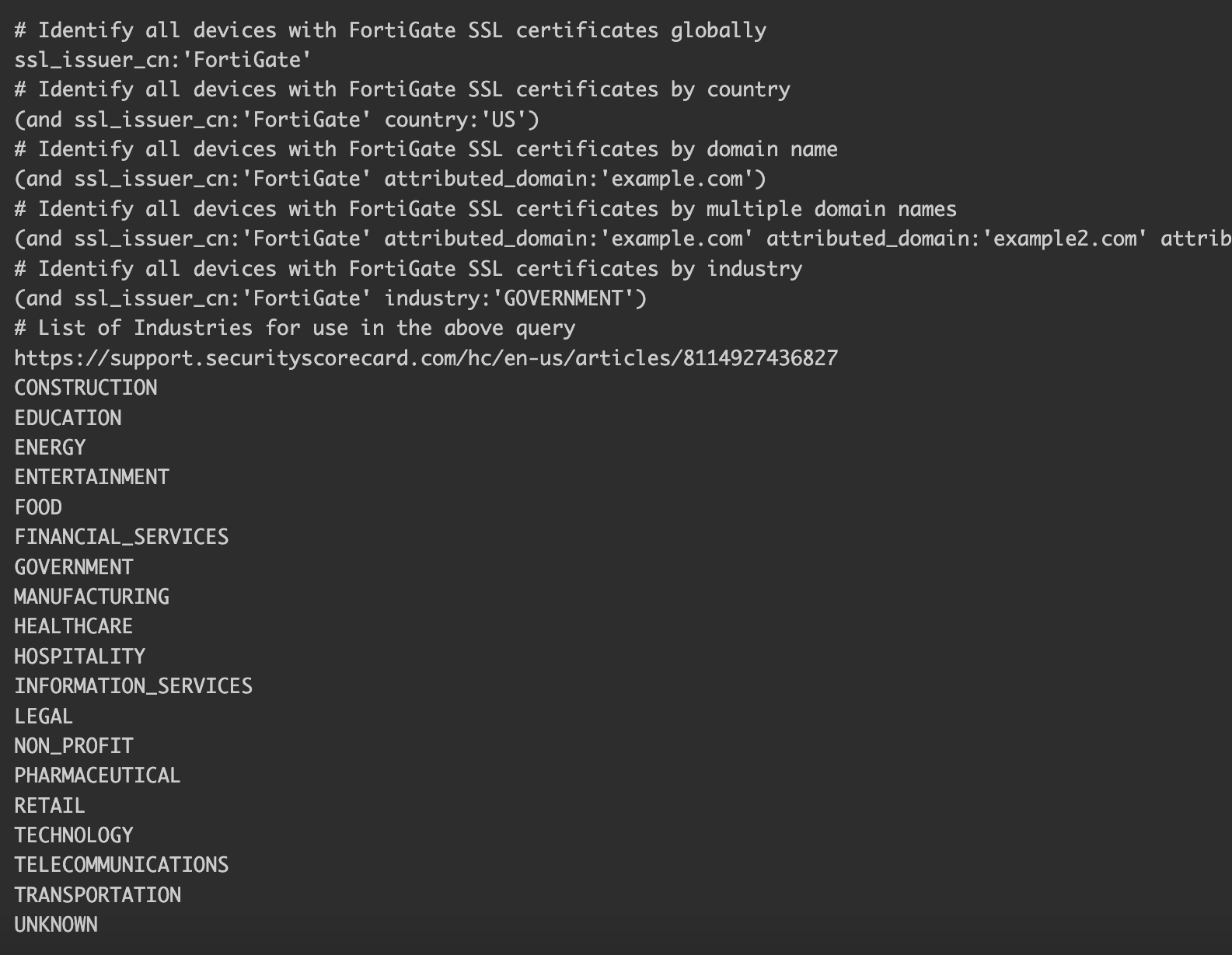
The following Attack Surface Intelligence search queries will display all Fortinet appliances hosting an SSL certificate issued by FortiGate that have been collected by SecurityScorecard sensors: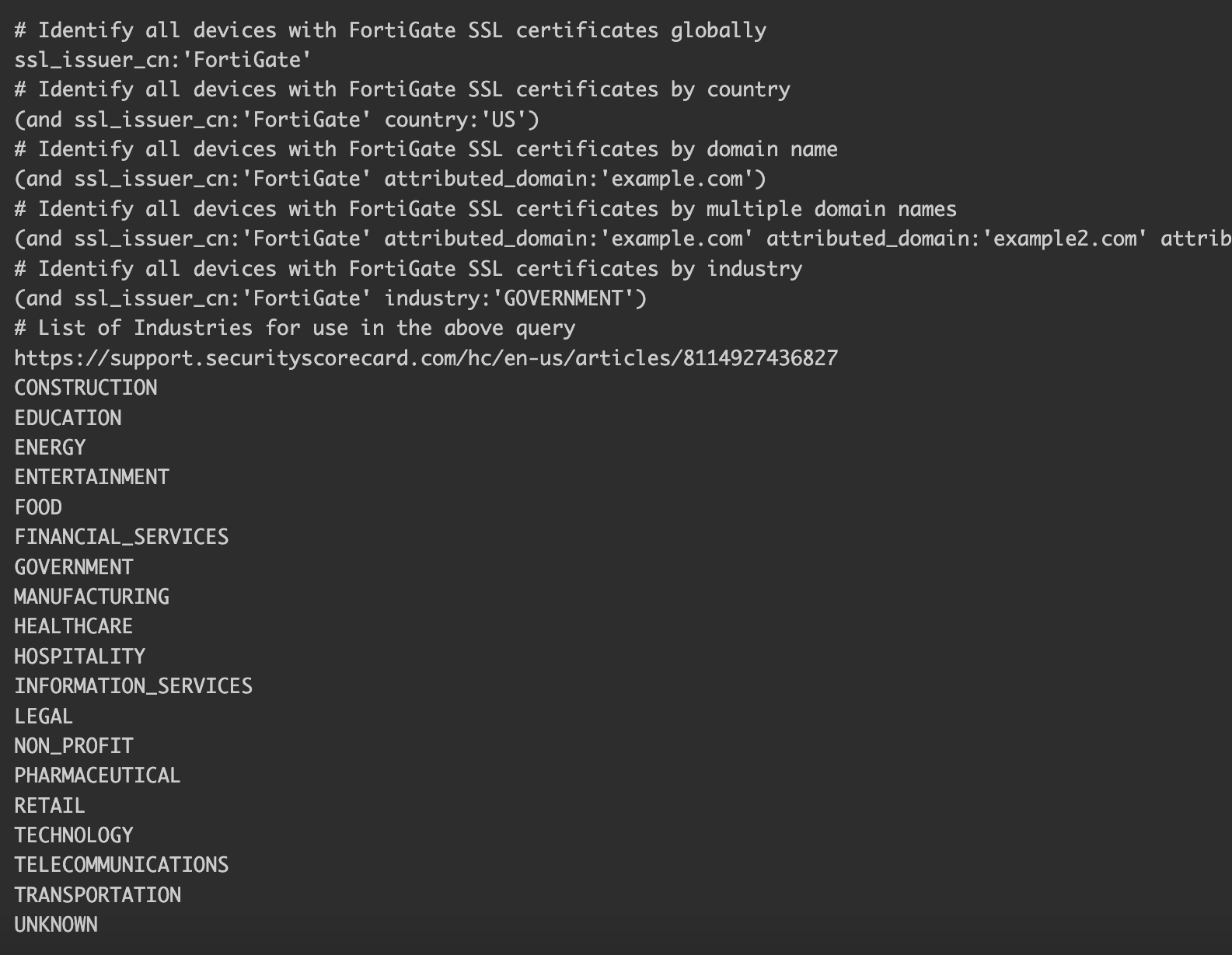
Test exposed Fortigate devices for vulnerability to CVE-2023-27997
To enhance the effectiveness of your organization’s proactive cybersecurity efforts against this threat, the recently released testing tool from Bishop Fox will be incredibly useful. This open-source Python script will help to determine whether a Fortigate device is vulnerable, patched, or facing another issue. We recommend exporting lists of Fortigate IP addresses related to your organization surfaced by ASI, and then running the Python script to test the identified IP addresses. You can find the tool here: BishopFox CVE-2023-27997 Testing Tool. We recognize and thank BishopFox for this valuable community resource and its efforts to help make the world a safer place. IMPORTANT: Please remember to only run the Bishop Fox CVE-2023-27997 Testing Tool on assets you own or have permission to test, such as devices on your own network or vendors/partners with whom you have existing relationships and agreements. Please contact your account manager if you have questions or need support in surfacing potentially vulnerable systems with Attack Surface Intelligence. Click here for more information or to request a demo of SecurityScorecard’s context-rich threat data platform, Attack Surface Intelligence.




