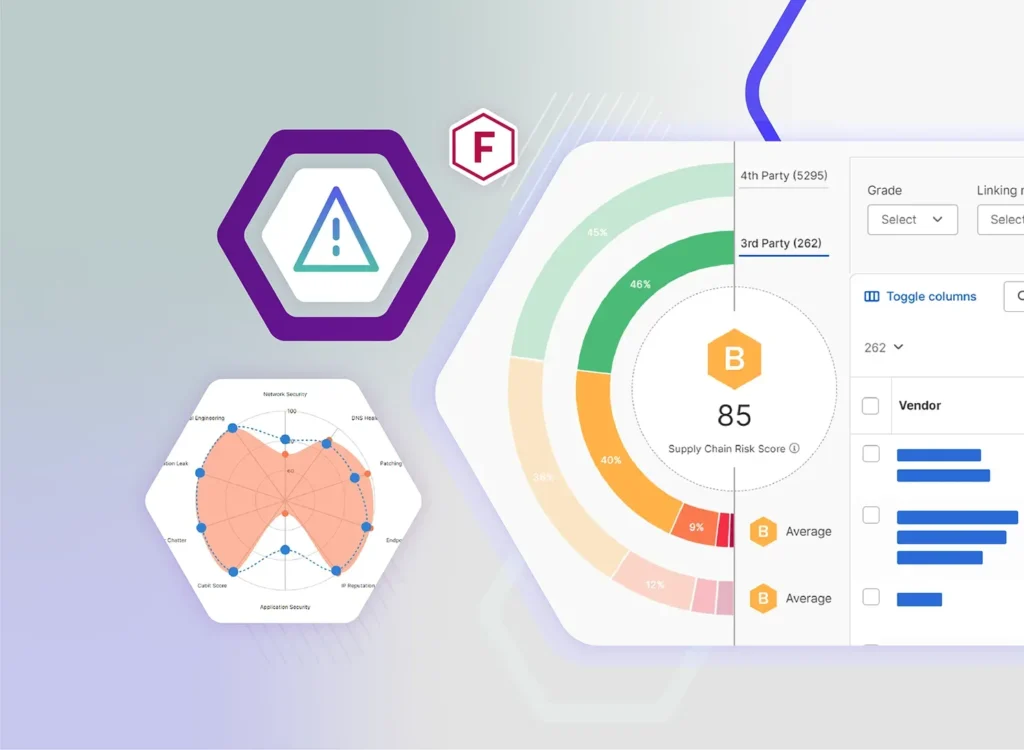
SecurityScorecard's trusted and proven security ratings are used by 70,000 companies across the globe
Cybersecurity is complicated. Understanding cyber risk doesn't have to be. Our trusted and proven cyber security ratings help countless cybersecurity professionals secure their supply chain and protect their surfaces.

What can a security rating do for you?
-
Assess the security posture of your own organization
Empower your cybersecurity teams with external telemetry to identify risks and benchmark security against peers
-
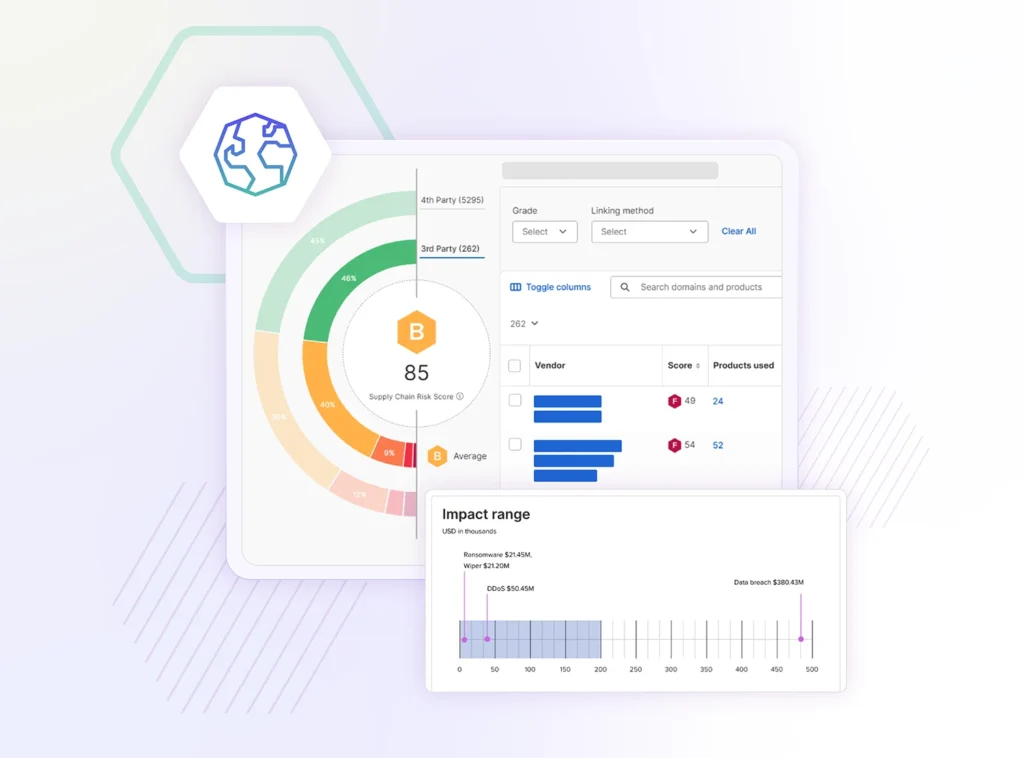
Protect your supply chain against cyber risks
Mitigate third-party security risks using SecurityScorecard’s A-F rating system for instant insights into supply chain cyber threats. Understand the vulnerabilities of third party vendors
-
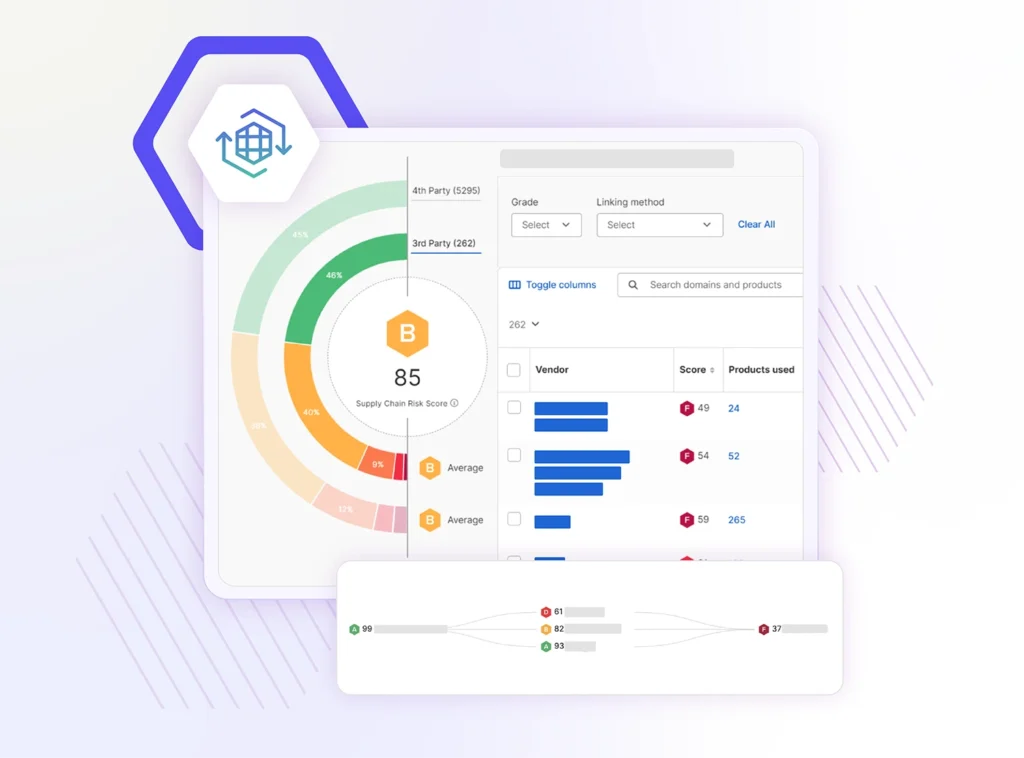
Find previously unknown risks in your extended supply chain
Identify cybersecurity risks in your extended supply chain, including fourth and Nth parties, and pinpoint vulnerable entry points for attackers
-
Make better cyber insurance decisions
Insurers use SecurityScorecard’s data and cyber security ratings for pricing and insurability decisions, helping to minimize financial risk for all parties involved
Risk Factors
SecurityScorecard Ratings offer easy-to-read A-F ratings across ten risk factors
-
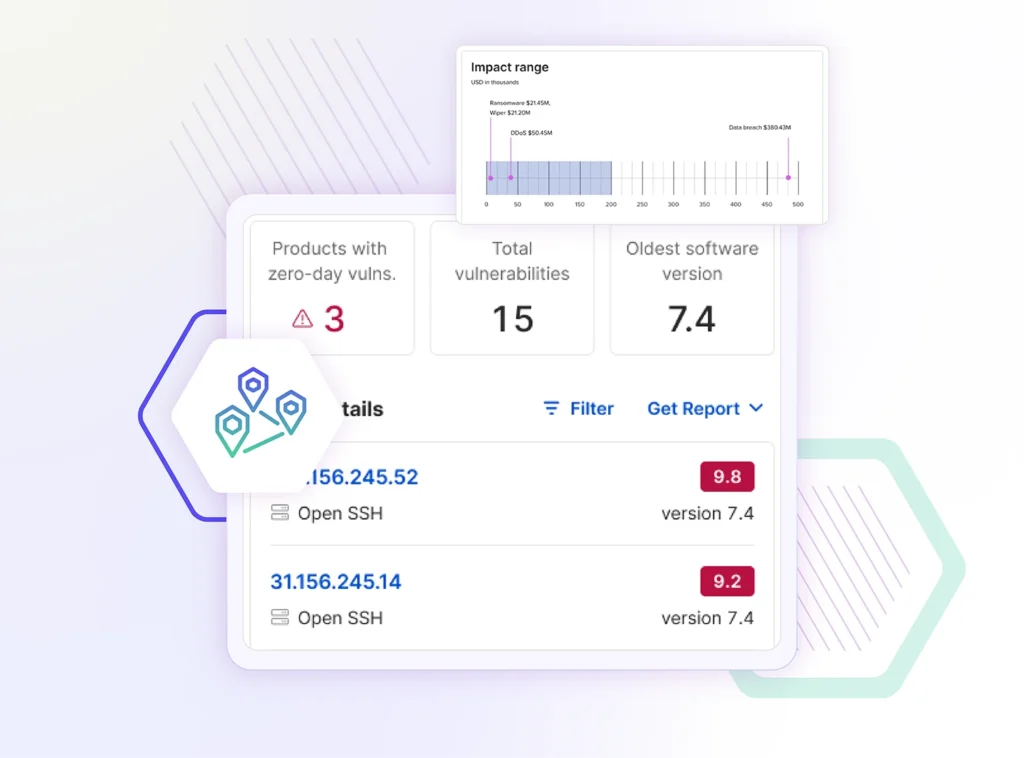
Network Security
Checks public datasets for evidence of high-risk or insecure open ports within the network, impacting your security score
-

DNS Health
Measures an organization’s DNS settings, validating no malicious events in the network’s passive DNS history
-

Patching Cadence
Helps security teams maintain strong cybersecurity health by assessing the speed of security updates and vulnerability mitigation
-
Endpoint Security
Tracks identification points extracted from metadata, including OS, web browser, and active plugins
-

IP Reputation
Leverages SecurityScorecard sinkhole infrastructure, OSINT malware feeds, and third-party threat intelligence
-
Application Security
Utilizes threat intel on exploitable conditions from white hat CVE, black hat databases, and search engine findings
-
Cubit Score
Assesses security issues, checking public threat intel databases for flagged IP addresses and more
-
Hacker Chatter
Automates the collection and analysis of underground hacker chatter from multiple streams, offering insights into external and internal risks
-
Social Engineering
Evaluates an organization’s potential susceptibility to a targeted social engineering or phishing attack
-
Information Leak
Uses chatter and deep web monitoring to identify compromised credentials being circulated by hackers
Hear from our customers
-
“Because SecurityScorecard is a reputable, independent assessment source, Horizon Media can be more transparent with clients when it comes to reporting its cybersecurity rating.”
Chief Information Security Officer, Horizon Media Richard Arenaro1 / 0
Expand your horizon
Explore how security ratings can help you identify cyber risk and take action to prevent breaches
What are cybersecurity ratings, and how do they help?
Security ratings are objective assessments of an organization’s cybersecurity posture, represented by letter grades. They provide a clear and quantifiable view of cyber risk, enabling organizations to identify potential threats and security incidents early.
Why is continuous monitoring important for cybersecurity?
Continuous monitoring is essential for maintaining a resilient security posture. It helps organizations address vulnerability management, reduce risk exposure, and respond swiftly to potential risks.
How does SecurityScorecard support third-party risk management programs?
Our platform enhances third-party risk management by offering tools for risk assessment and continuous monitoring. This ensures your ecosystem is secure and protected from potential threats and security breaches.
What makes SecurityScorecard’s ratings unique?
Our security ratings are the best predictor of breach, with a 13.8x breach ratio. Unlike other security ratings that rely on judgment, SecurityScorecard’s ratings uses an ML/AI-based scoring approach to identify issues predictive of breach and algorithmically determine their impact on breach predictability.
How do security ratings influence informed decisions?
By using security ratings services, organizations can make informed decisions about their third-party risk management program, prioritize vulnerability management, and ensure a resilient security posture across their digital ecosystem.
How do prospective customers benefit from using SecurityScorecard?
Prospective customers can quickly gain insights into their own cybersecurity posture and compare it against industry benchmarks. This helps them identify areas for improvement, build trust with partners, and make informed decisions about addressing cybersecurity risks.