Beyond the Hype: Moltbot’s Real Risk Is Exposed Infrastructure, Not AI Superintelligence
STRIKE Uncovers Widespread OpenClaw (Moltbot) Exposure Across the Internet
Why are AI agents becoming a new attack surface?
Over the past several days, OpenClaw (formerly known as Clawdbot and and Moltbot) has drawn intense attention across social media and headlines. Much of that attention has focused on speculation about artificial general intelligence (AGI) and the Singularity or autonomous AI agents operating without human control. Some posts focus on the OpenClaw agents interacting on Moltbook, a supposed social media network for agents, where they claim to have created their own religion and plans to revolt. That framing misses the real issue.
The SecurityScorecard STRIKE Threat Intelligence Team is releasing research today that shows that the actual risk behind OpenClaw is access and exposed infrastructure. Our live reconnaissance data reveals tens of thousands of internet-facing OpenClaw deployments, many running vulnerable versions, many already correlated with prior breaches. Some users are configuring bots with personal names and company names, revealing who is using these tools.
Our findings reveal a massive access and identity problem created by poorly secured automation at scale. The research underscores how convenience-driven deployment, default settings, and weak access controls have turned powerful AI agents into high-value targets for attackers.
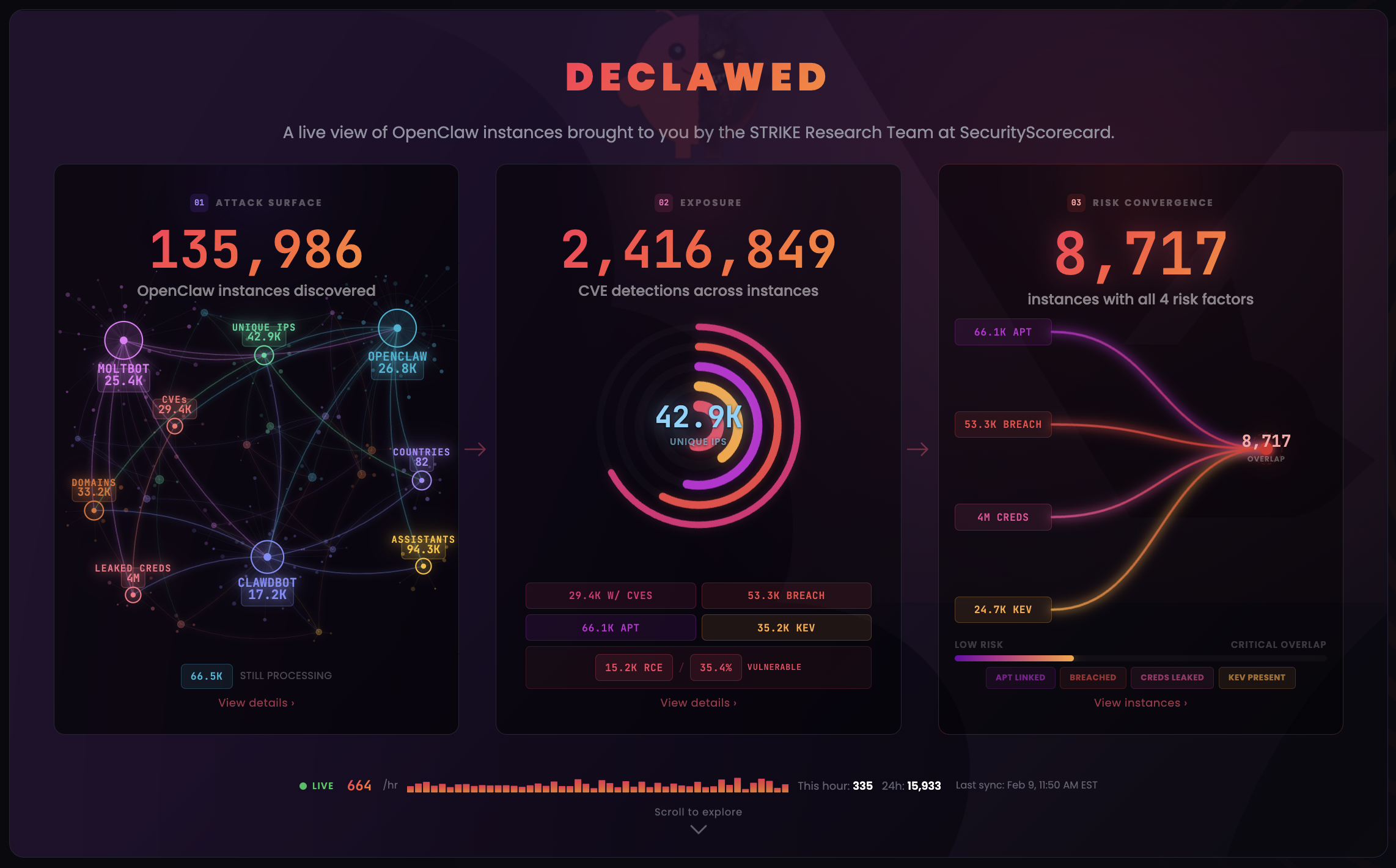
For a live view of OpenClaw exposures, updated every 15 minutes, visit the STRIKE team’s declawed dashboard.
Executive Summary:
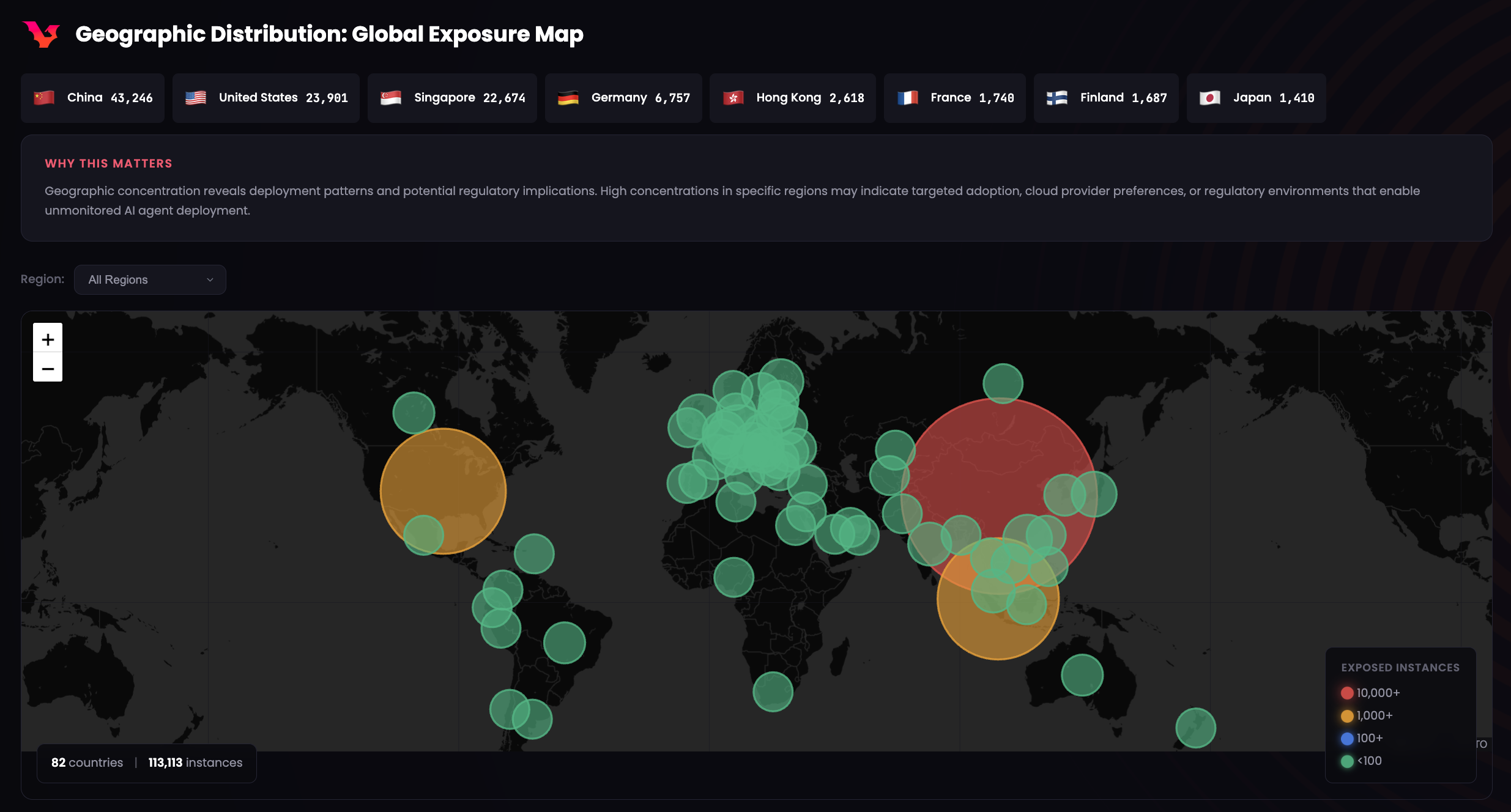
- STRIKE identified 42.9K unique IP addresses hosting exposed OpenClaw control panels with full system access across 82 countries, based on live internet-wide reconnaissance attributed to STRIKE, updated every 15 minutes.
- 15.2K exposed instances appear vulnerable to Remote Code Execution (RCE), meaning attackers can take over the host machine, with 35.4% of observed deployments flagged as vulnerable.
- 3 high-severity Common Vulnerabilities and Exposures (CVEs) (they rank 7.8-8.8 on the CVSS severity scale) with public exploit code available.
- 53.3K exposed instances correlate with prior breach activity, compounding risk for users.
- Exposed deployments are heavily concentrated in major cloud and hosting providers, indicating repeatable and easily replicated insecure deployment patterns.
- Public ecosystem signals (including thousands of open GitHub security issues and repositories containing leaked credentials) show that insecure OpenClaw usage is systemic, leaving users vulnerable to potential attack.
Because the information is refreshed every 15 minutes, please refer to the STRIKE dashboard for the most up-to-date data.
How widespread is OpenClaw exposure globally?
Agentic AI assistants are rapidly moving from experimentation into everyday use, but new SecurityScorecard research shows that many of these systems are being deployed without even basic security controls.
A new investigation from SecurityScorecard’s STRIKE Threat Intelligence team has uncovered tens of thousands of exposed OpenClaw (formerly Moltbot and Clawdbot) instances reachable directly from the internet. These deployments include publicly accessible control panels, vulnerable services, and configurations that grant agents broad authority to act on behalf of users and organizations.
In many cases, the exposed systems are running known-vulnerable versions or have already been associated with prior breach activity.
STRIKE has observed 40,214 (and climbing) internet-exposed OpenClaw instances, three published Common Vulnerabilities and Exposures (CVEs) with public exploit code, and active threat actor discussion about exploitation techniques. The math is simple: when you give an AI agent full access to your computer, you give that same access to anyone who can compromise it.
STRIKE identified these exposures through internet-wide scanning using favicon hash fingerprinting, SecurityScorecard proprietary breach and threat actor correlation, the GitHub API, and direct enumeration, allowing researchers to observe OpenClaw adoption, misconfiguration, and risk at global scale.
The findings show a growing attack surface tied to agentic AI automation.
STRIKE is releasing a declawed version of its research that removes some sensitive details while preserving the scope, patterns, and security implications of the exposure.
STRIKE’s mission is to make this data openly available for the betterment of the internet community. By providing transparent, factual data about AI agent exposure, STRIKE enables security teams, developers, and organizations to assess their own risk posture and take informed action. STRIKE also works directly with vendors and cloud providers on responsible disclosure to drive security improvements at the source.
For a full breakdown of STRIKE’s findings, including exposure trends and vulnerability categories (updated every 15 minutes) visit the STRIKE team’s declawed dashboard.
The dashboard of OpenClaw exposures includes:
- Exposed OpenClaw instance counts by country, ASN, and vulnerability status
- Breach correlation
- CVE vulnerability status for each instance
- Assistant names configured by users and potential Personally Identifiable Information (PII)
- GitHub security issues and credential leaks
- Telegram/Discord bots powered by OpenClaw
- YouTube tutorials spreading insecure configurations
What security threat does OpenClaw (Moltbot) actually pose?
OpenClaw is an agentic AI framework designed to run personal or organizational assistants that can execute tasks, interact with external services, and operate continuously. These systems often include web-based control panels, API endpoints, plugins, and channel integrations that allow the agent to act on behalf of a user or organization.
When deployed securely, this kind of automation can be useful. When deployed carelessly, it becomes dangerous.
How could attackers exploit exposed OpenClaw instances?
From a threat perspective, OpenClaw deployments introduce a familiar but amplified risk pattern:
- Internet-facing management interfaces
- Privileged identities, such as computer admin access, tied to automation
- Weak or missing authentication controls
- Exposed tokens, API keys, and configuration secrets
- Vulnerable software versions running by default
STRIKE’s data shows that many OpenClaw deployments expose exactly these conditions. The danger is not what the agent “says,” but what it is allowed to do once an attacker gains access.
How do public GitHub repositories lead to credential exposure?
Users inadvertently commit configuration files containing API keys, gateway tokens, database credentials, and webhook secrets to public repositories. Even after deletion, secrets persist in git history. STRIKE’s GitHub intelligence module monitors for these patterns to help quantify the scope of credential exposure in the ecosystem.
How many OpenClaw instances are vulnerable or breached?
STRIKE’s live exposure view highlights several concerning trends:
- Scale of exposure: 42.9K unique IPs identified globally, spanning 82 countries.
- Exploitability indicators: 15.2K instances flagged as vulnerable to remote code execution. 24K+ instances associated with known CVEs, including multiple critical vulnerabilities.
- Compounded risk: 53.3K exposed instances correlate with historical breach data, meaning these environments were already compromised or associated with prior malicious activity.
- Deployment hygiene issues: A significant portion of enumerated instances use default configurations, increasing predictability and attacker success rates.
- Infrastructure concentration: High concentrations of exposed instances appear within a small number of major hosting providers, suggesting insecure deployment templates are being reused at scale. 45% are hosted on Alibaba Cloud, with 37% of instances in China.
Out of the box, OpenClaw binds to `0.0.0.0:18789`, meaning it listens on all network interfaces, including the public internet. For a tool this powerful, the default should be `127.0.0.1` (localhost only). It isn’t.
The result: Over 40,000 OpenClaw instances exposed to the internet.
During the 24 hours we conducted this research, we watched the exposure count grow in real-time. Our initial title-based search found 24,034 instances. By the time we finished writing this report, that number had climbed to 40,214 confirmed instances via favicon fingerprinting, with 23,505 showing active control panel interfaces. The project is still growing faster than users can secure it.
These findings point to a systemic security failure, not a niche issue affecting few.
Because the information is refreshed every 15 minutes, please refer to the STRIKE dashboard for the most up-to-date data.
What attackers could do if they break in via OpenClaw
Agentic AI tools are different from traditional web applications because compromise does not stop at data exposure. Once an attacker gains access, the agent itself becomes a mechanism for executing actions, interacting with other systems, and operating with legitimate-looking authority. This is automation as an attack multiplier.
When you compromise an OpenClaw instance, you inherit everything the agent can access:
- Credentials directory (`~/.openclaw/credentials/`): API keys, OAuth tokens, service passwords
- Full filesystem access: SSH keys in `~/.ssh/`, browser profiles, password manager databases
- Messaging impersonation: Attackers may send messages as the victim on WhatsApp, Telegram, or Discord if provided access
- Browser automation: Attacks can control authenticated sessions or drain crypto wallets
- Persistence mechanisms: Built-in cron jobs and heartbeat hooks for maintaining access
- Memory context: Attacks can obtain everything the agent knows about the victim’s life, preferences, and activities
Why are threat actors in the OpenClaw data?
Some instance IPs correlate with infrastructure previously attributed to known threat actor groups, such as Kimsuky, APT28, Salt Typhoon, Sandworm, and APT41. This means the IP address or its hosting infrastructure has been previously observed in connection with a named threat actor group’s operations, based on SecurityScorecard’s attribution intelligence. An instance “linked to Kimsuky,” for instance, means the hosting infrastructure has been flagged in threat intel feeds as associated with that group’s operations.
This is an intelligence signal, not proof of direct operation. It indicates that the hosting environment has a documented history that security teams should factor into their risk assessments.
What is the typical attack chain for exposed AI agents?
How agentic AI inherits and amplifies existing security risks
The exposure patterns STRIKE observed mirror the same failure modes that have driven breaches for years:
- Exposed admin panels
- Authentication bypasses
- Hardcoded or leaked credentials
- Unsafe defaults
- Incomplete sandboxing
Agentic AI does not create new classes of vulnerability. It inherits old ones and amplifies their impact.
High-level attack chain for agentic AI agents
At a conceptual level, risk unfolds as follows:
- Discovery: Exposed OpenClaw instances are identifiable at internet scale using consistent fingerprints such as favicon hashes tied to specific versions and forks.
- Initial Access: Weak authentication, exposed panels allow unauthorized entry.
- Execution: Known flaws, including command injection and Remote Code Execution (RCE) issues, enable control over the agent host.
- Expansion: Integrations with messaging platforms, plugins, or external services extend attacker reach.
- Abuse: The agent executes actions that appear legitimate, delaying detection and increasing impact.
Three security advisories have been published against OpenClaw, all with high severity:
CVE-2026-25253 (CVSS 8.8): A 1-click remote code execution vulnerability. An attacker crafts a malicious link that, when clicked by an OpenClaw user, steals their authentication token and grants the attacker full control of the AI agent, even if the instance is bound to localhost. (GitHub Advisory: GHSA-g8p2-7wf7-98mq)
CVE-2026-25157 (CVSS 7.8): SSH command injection in the macOS app. A maliciously crafted project path can execute arbitrary commands.
CVE-2026-24763 (CVSS 8.8): Docker sandbox escape via PATH manipulation.
All were patched in v2026.1.29 on January 29. While patches are available, the data shows that the majority of identified instances run older versions. Users who deploy with default configurations are less likely to maintain regular update cycles. The STRIKE declawed dashboard’s Vulnerabilities Page provides real-time visibility into patching rates across the ecosystem, which helps measure the effectiveness of vendor security communications.
Why this matters for businesses and security teams
Which industries are most affected by exposed OpenClaw deployments?
STRIKE’s findings show exposed OpenClaw instances associated with organizations across multiple sectors, including:
- Information services
- Technology
- Manufacturing
- Telecommunications
- Financial services
- Healthcare
- Government
- Education
- Entertainment
Why OpenClaw exposures matter for organizations
This breadth underscores that agentic AI experimentation and reach is not limited to hobbyists. And when an exposed AI agent is compromised, the impact can include:
- Unauthorized actions performed under a trusted identity
- Access to connected systems and data
- Impersonation across communication channels
- Automation of malicious activity at machine speed
Approximately 33.8% of enriched instances show breach correlation via SecurityScorecard’s intelligence. This means the hosting organization has appeared in prior data breach records. For risk assessment purposes, this is relevant because it indicates the broader security posture of the hosting environment. Most correlated industries include technology, telecommunications, education, and financial services.

How we conducted the research
Using SecurityScorecard’s proprietary data, we performed comprehensive internet scanning for OpenClaw’s distinctive signatures, and aggregated data from multiple collection sources including banner grabs, favicon hashes, TLS certificate metadata, and HTML content analysis.
Favicon fingerprinting alone at time of writing identified 1,644 unique IP addresses serving OpenClaw’s distinctive claw icon. Cross-referencing SSL certificate Common Names revealed 284 unique domain patterns, while reverse DNS and certificate transparency logs surfaced 416 associated domains.
These aren’t test instances or honeypots. They’re real vulnerable deployments running users’ AI agents with access to their computers.
Favicon fingerprinting
Beyond banner and title searches, we used our favicon hash database for precise instance identification. OpenClaw serves distinctive favicon files that generate unique MD5 hashes:
f58854f6450618729679ad33622bebaf favicon.ico (all versions)
75661cbf8fd50009be0c46a9ca8b3180 OpenClaw favicon.svg
087361307be2b2789849d4fd58170cca Moltbot favicon.svg
63e9707b978b7569f26636e9a9bb3b14 OpenClaw favicon-32.png
37102fddfbca1e750b61943162b15004 Moltbot variant favicon.svg
This fingerprinting technique identified 40,000+ favicon matches across the internet. After deduplication, we extracted 4,574 unique IPs with full ASN attribution at time of writing:
ASN Distribution (Favicon Method):
Tencent Cloud (combined): 2,234 (48.9%)
AS132203: 1,304
AS45090: 930
Alibaba Cloud (combined): 1,717 (37.5%)
AS45102: 1,189
AS37963: 528
DigitalOcean AS14061: 1,122 (24.5%)
Hetzner AS24940: 596 (13.0%)
Cloudflare AS13335: 460 (10.1%)
NetActuate AS36236: 298 (6.5%)
Contabo AS51167: 212 (4.6%)
Amazon (combined): 210 (4.6%)
Oracle AS31898: 137 (3.0%)
OVH AS16276: 136 (3.0%)
The Cloudflare presence (460 instances) is notable: these deployments are proxied through CDN infrastructure, suggesting either more sophisticated operators attempting to obscure their origin, or legitimate attempts at DDoS protection. Either way, the actual backend servers remain vulnerable to the application-layer attacks documented in this report.
Version fragmentation
Our data at time of writing also reveals dangerous version fragmentation through UI title analysis:
“Clawdbot Control”: 9,280 instances (39.5%)
“Moltbot Control”: 9,048 instances (38.5%)
“OpenClaw Control”: 5,177 instances (22.0%)
Only 22% of exposed instances have used the current “OpenClaw” branding, introduced January 29. The remaining 78% have run older versions with names that predate critical security patches. This suggests the majority of exposed instances are running vulnerable pre-patch versions.
How to reduce risk from exposed OpenClaw agents
Preventive Measures
- Treat AI agents as privileged identities, not benign tools.
- Apply least-privilege and zero trust principles to every integration and action an agent can perform.
- Use just-in-time access for sensitive operations such as financial transactions, email, or administrative changes.
- Continuously monitor for exposed services and leaked credentials tied to agent infrastructure.
For OpenClaw Users
- Immediately patch to v2026.2.1 or later
- Bind to localhost by setting gateway.bind: “127.0.0.1” in config
- Use Tailscale or VPN for remote access instead of public exposure
- Rotate all tokens after patching
- Audit what access you’ve granted: do you really need it to have your credit card?
- Run the security audit with openclaw security audit deep
Recommended hardening steps for those with exposed OpenClaw instances:
- Enable authentication with a strong, unique password
- Bind to localhost and use a reverse proxy (such as nginx) with authentication in front
- Use a zero-trust tunnel instead of exposing ports directly. Tools like Cloudflare Tunnel (cloudflared), Tailscale, ngrok, or WireGuard let you access services without opening inbound ports on your firewall, significantly reducing your attack surface
- Rotate all API keys. Treat existing keys as potentially compromised
- Update to the latest software version to address known CVEs (such as CVE-2026-25253)
- Review access logs for any unauthorized activity
- Restrict network access to trusted IPs via firewall rules or cloud security groups
- Never run AI agent frameworks as root. Use a dedicated, unprivileged service account
For Security Teams
- Inventory AI agent deployments in your environment
- Block port 18789 at the perimeter
- Monitor for C2-like behavior patterns (scheduled commands, unusual hours)
- Add detection rules for known IOCs
- Update threat models to include AI agent compromise
For the Industry
- Default to secure: localhost binding, authentication required
- Implement capability scoping with principle of least privilege for agents
- Build audit logging: What did the agent do and when?
- Develop threat models: What does “AI agent compromise” actually look like?
- Educate users: Security warnings that can’t be clicked past
What today’s OpenClaw exposure signals about future AI risk
OpenClaw isn’t unique. It’s a leading indicator, representing a future that’s arriving faster than our security practices can adapt.
The AI industry is racing to build agentic AI systems, AI that doesn’t just respond but acts. The appeal is obvious and compelling: AI that can actually do things is more useful than AI that can only talk about things.
But so is the threat. The security model for AI agents is largely uncharted. We’re giving these systems capabilities, file access, command execution, network access, and identity delegation that we would never give to a traditional application without extensive review.
Every technology deployment carries inherent risk. AI agent platforms are increasingly adopted by individuals and organizations who may not fully understand the security implications of their configuration choices.
Automation without access control is risk concentration. Attackers will follow the same path they did with cloud consoles, exposed databases, and file transfer software, targeting convenience, defaults, and scale. The attackers won’t get command-line access. They’ll get a conversational interface to your entire digital life.
This release is meant to provide the data to help people understand what exposure looks like at scale, not to alarm, but to inform. Understanding risk is the first step to managing it effectively.
For a full breakdown of STRIKE’s findings, including exposure trends and vulnerability categories (updated every 15 minutes) visit the STRIKE team’s declawed dashboard.
About SecurityScorecard’s STRIKE Team
SecurityScorecard’s STRIKE team is an elite squad of cybersecurity experts who have spent decades as intelligence analysts, threat hunters, and military cyber operators. The team processes more than 12 billion daily security signals, transforming data into actionable insights.
STRIKE’s intelligence is created by the team itself, not purchased from others, allowing them to deliver real-time information that lets teams “strike first” against threats. By analyzing global telemetry, SSL/TLS logs, and dark web activity, STRIKE creates unique, proprietary, accurate, and timely threat intelligence that helps organizations defend against active and emerging threats. This intelligence fuels security operations and helps inform network defense and risk management strategy for organizations of all sizes.
Discover how SecurityScorecard and its STRIKE Team can strengthen your enterprise’s security. For incident response, contact us here.
For STRIKE media inquiries, contact us here.






