SecurityScorecard on AWS
Proactively Detect Global Threats in Your Ecosystem Before Disruption
SecurityScorecard powered by AWS mitigates breach risk and provides actionable details for every issue surfaced. Instantly gain a holistic view of any organization’s cyber risk.

SecurityScorecard Works With AWS to Help You Stay Ahead of Threats
Blog: SecurityScorecard and AWS Help Make Secure Software Procurement Faster and Easier
Blog: Up Level Your Amazon Security Lake with Attack Surface Intelligence
MSSP L1 for AWS: Managed Security starts at Level 1
See SecurityScorecard’s security posture: Vendor Insights profile on AWS Marketplace
Deploy SecurityScorecard in Minutes on AWS Marketplace
One Platform, Many Use Cases
Gain visibility of digital assets residing within disparate cloud and IoT ecosystems as your organization undergoes digital transformation.
Evolve your third-party and supply-chain risk management capabilities to scale your operations.
Maintain cybersecurity compliance so your organization can operate sustainably and qualify for new business in highly-regulated segments.
Gain an immediate view of any organization’s security posture to enable fast, risk-based decision-making.
Provide executives and boards with a holistic view of your cybersecurity and compliance posture.
Prioritize cybersecurity reviews with continuous monitoring to identify who is most at risk.
Helps brokers, insurers, and reinsurers work with stakeholders to reduce risk.
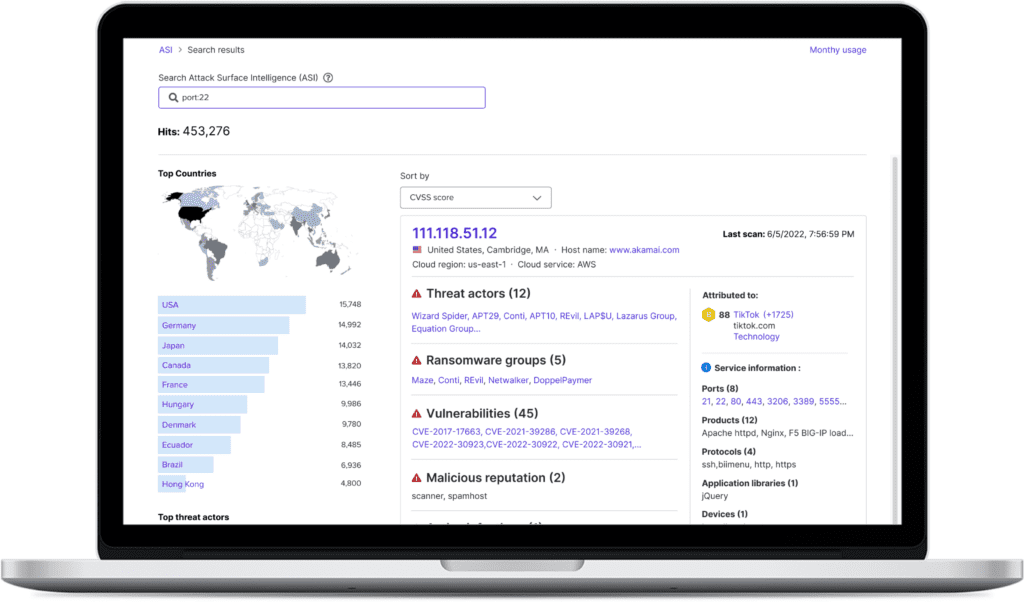
Intelligence Built By Threat Researchers For Threat Researchers
SecurityScorecard is a data company, first and foremost, building contextual intelligence to power its scorecards. We have built the most comprehensive data collection and attribution infrastructure over a decade, giving customers the most relevant, actionable, and trusted cyber risk information.
When data volume, quality, and speed matter, turn to SecurityScorecard’s threat intelligence. Gain confidence in knowing the intelligence collected is engineered for you to prevent future disruptions with unrivaled, up-to-date, and precision-built data.
Use AWS Cloud Credits to Improve Your Security Posture
Maximize your AWS investment by leveraging Enterprise Discount Program [EDP] credits to take control of your cybersecurity risk ecosystem. SecurityScorecard delivers an instant 360-degree view of any organization’s cyber risk using non-intrusive and proprietary data collection methods.

