Security Ratings That Reflect Real-Time Risk
We Do Ratings Differently – Built on Real-Time Intelligence
Precision Ratings for a Borderless Ecosystem
TITAN AI analyzes billions of data points daily and sinkholing 2B+ malware requests per day to provide a transparent, outside-in view of security posture that correlates directly to breach likelihood.
The TITAN AI Advantage
- Unmatched Signal Depth: We scan 4.1B IPs and domains to ensure your rating reflects reality.
- Continuous Monitoring: TITAN AI ratings update continuously, catching critical security regressions more frequently that provides a common language for risk.
- Trust Through Transparency: Our fair and accurate methodology allows every rated entity to see exactly what drives their score, ensuring data integrity.
13.8x
companies with a poor rating are 13.8x more likely to suffer a breach.

Gaps in Traditional Risk Assessments
The Visibility Gap
You can’t protect what you can’t measure. Static risk data leaves you vulnerable to shadow IT risks in your ecosystem.
Subjective Overload
Manual risk tiering is inconsistent. Without a standardized rating, technical debt and critical vulnerabilities go unprioritized.
Slow Response
When a zero-day hits, you don’t have time to send a survey. You need an instant rating filter to see who is impacted now.

Inside TITAN AI Ratings
We don’t just give you a letter grade – we give you the “why” behind the risk. We’re committed to giving you full visibility into our ratings.
- Risk Factors
- Benchmarking
- Detection
- Analytics
- Signals
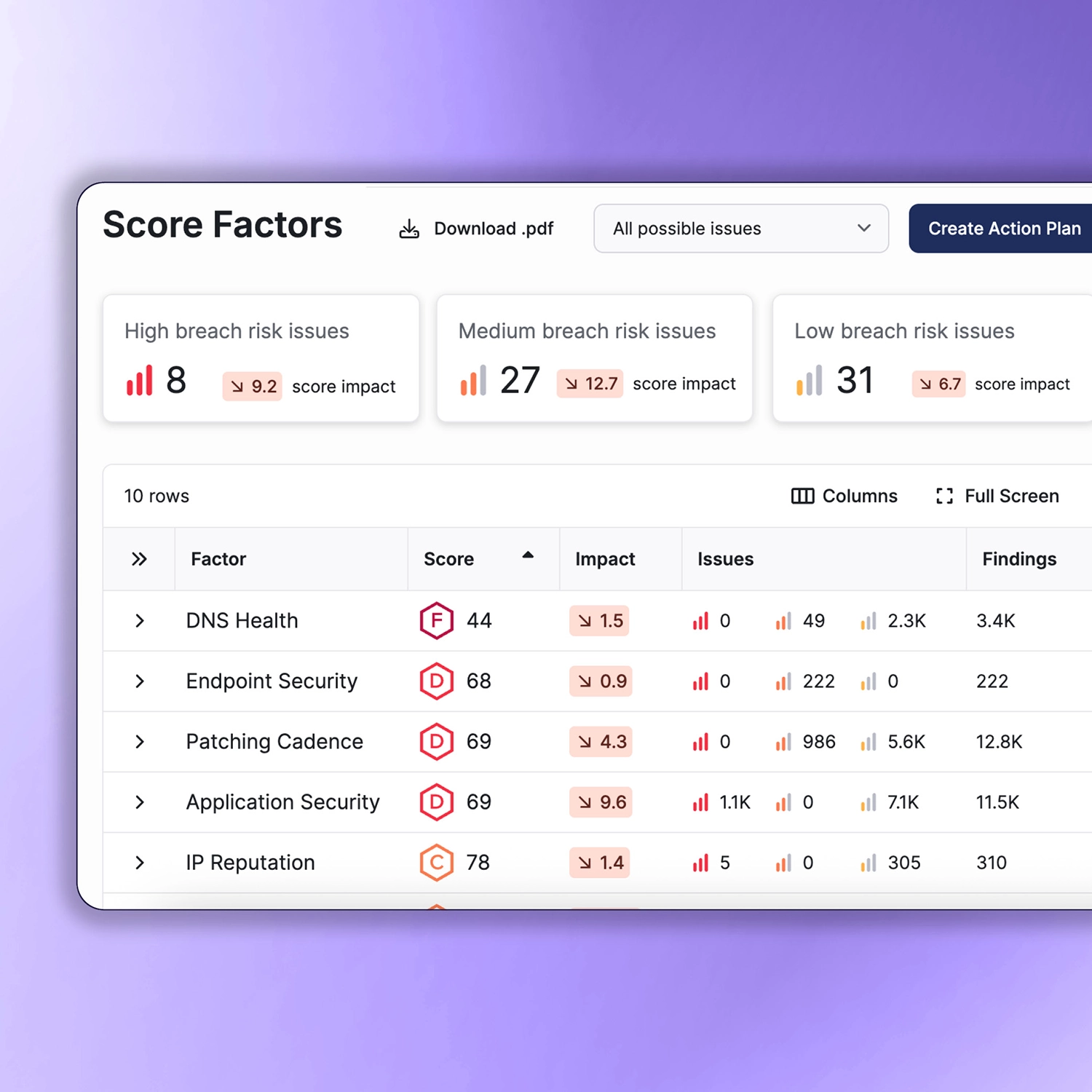
Risk Factor Breakdown
- Detailed visibility into 10 key categories, including DNS Health, IP Reputation, and Patching Cadence, to isolate specific weaknesses
- Understand how each individual risk factor contributes to your overall grade compared to industry-standard security benchmarks
- Connect high-level ratings to specific CVEs and misconfigurations that are actively lowering your organization’s security posture
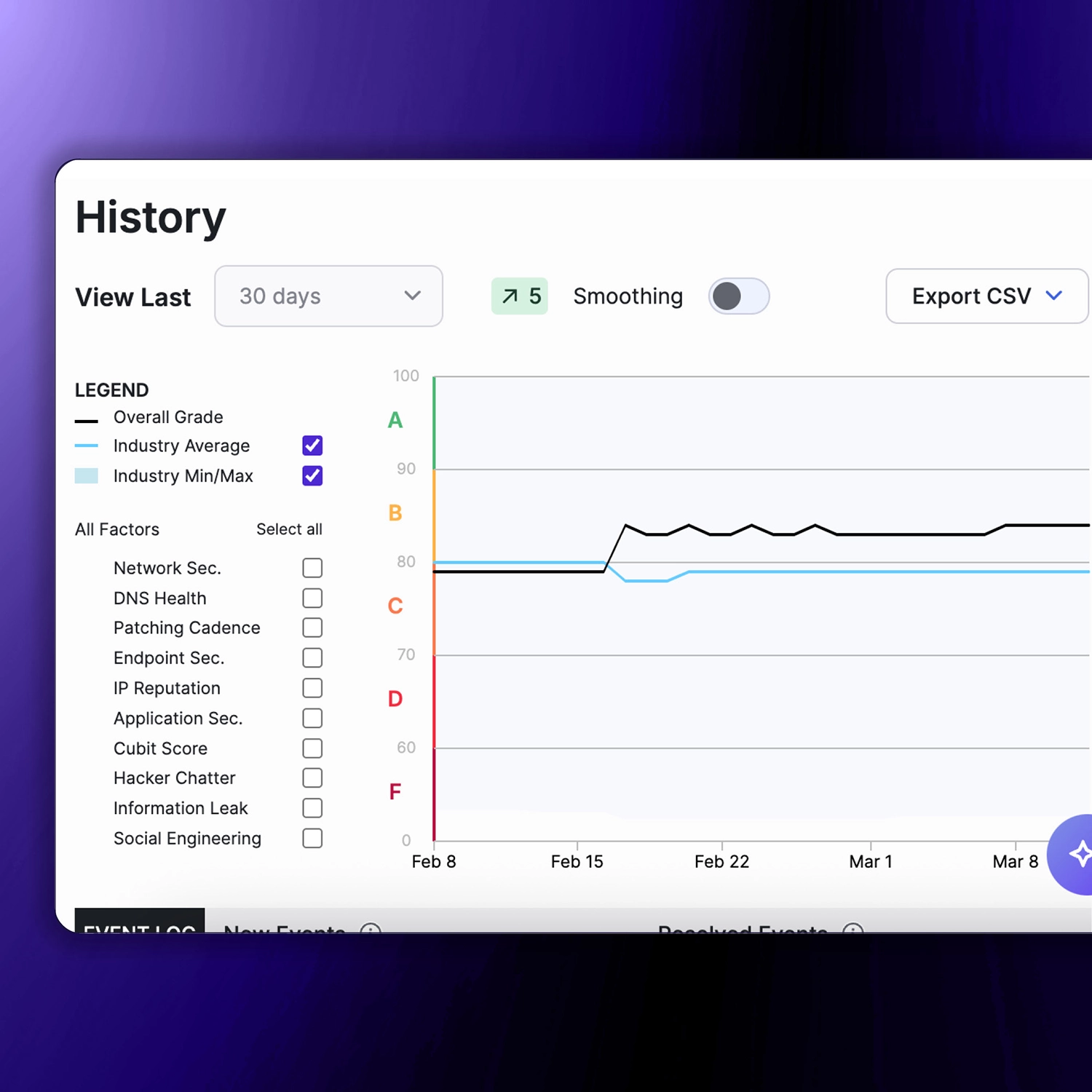
Historical Benchmarking
- Monitor rating trends over time to prove the ROI of security investments and visualize long-term improvements
- Compare your security trajectory against industry competitors to ensure your defenses remain ahead of the market average
- Map historical score fluctuations to internal changes or external global threats to identify patterns in your risk profile
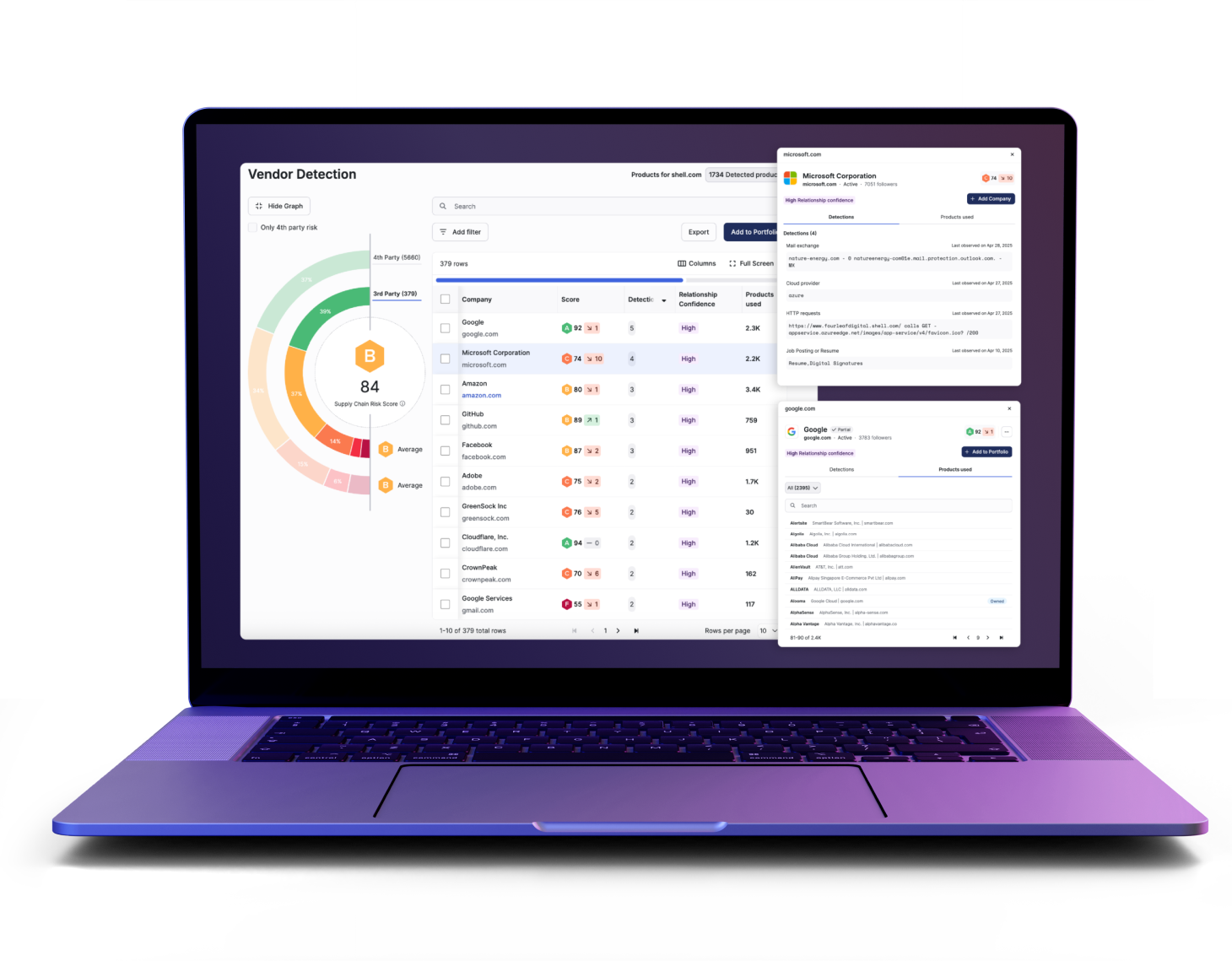
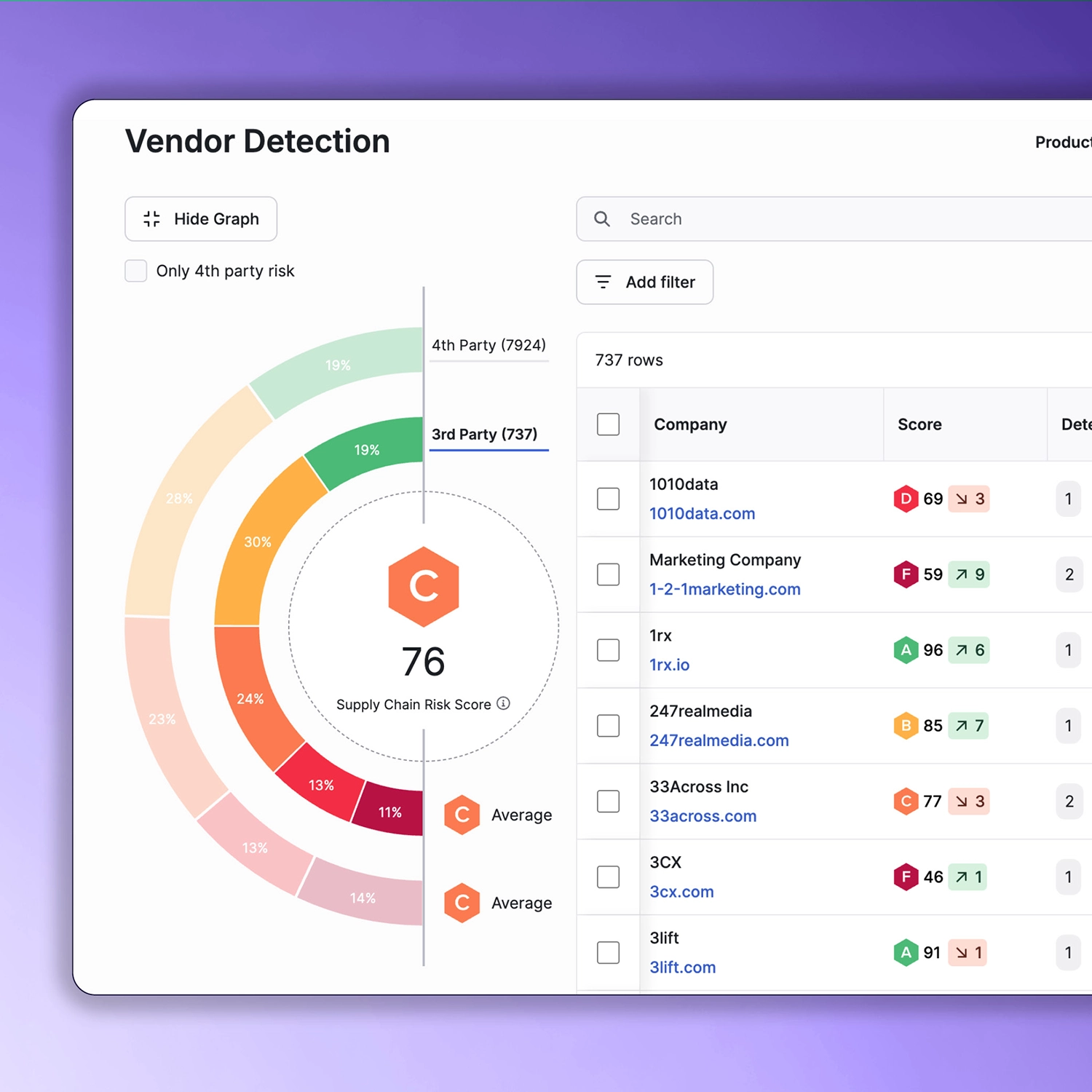
Automatic Vendor Detection
- Automatically identify 3rd and 4th-party vendors through advanced DNS and web crawling to eliminate “shadow” supply chain risk
- Maintain a real-time, self-updating list of active suppliers without relying on manual entry or outdated procurement spreadsheets
- Identify common fourth-party dependencies across your vendor base to prevent systemic outages from a single point of failure
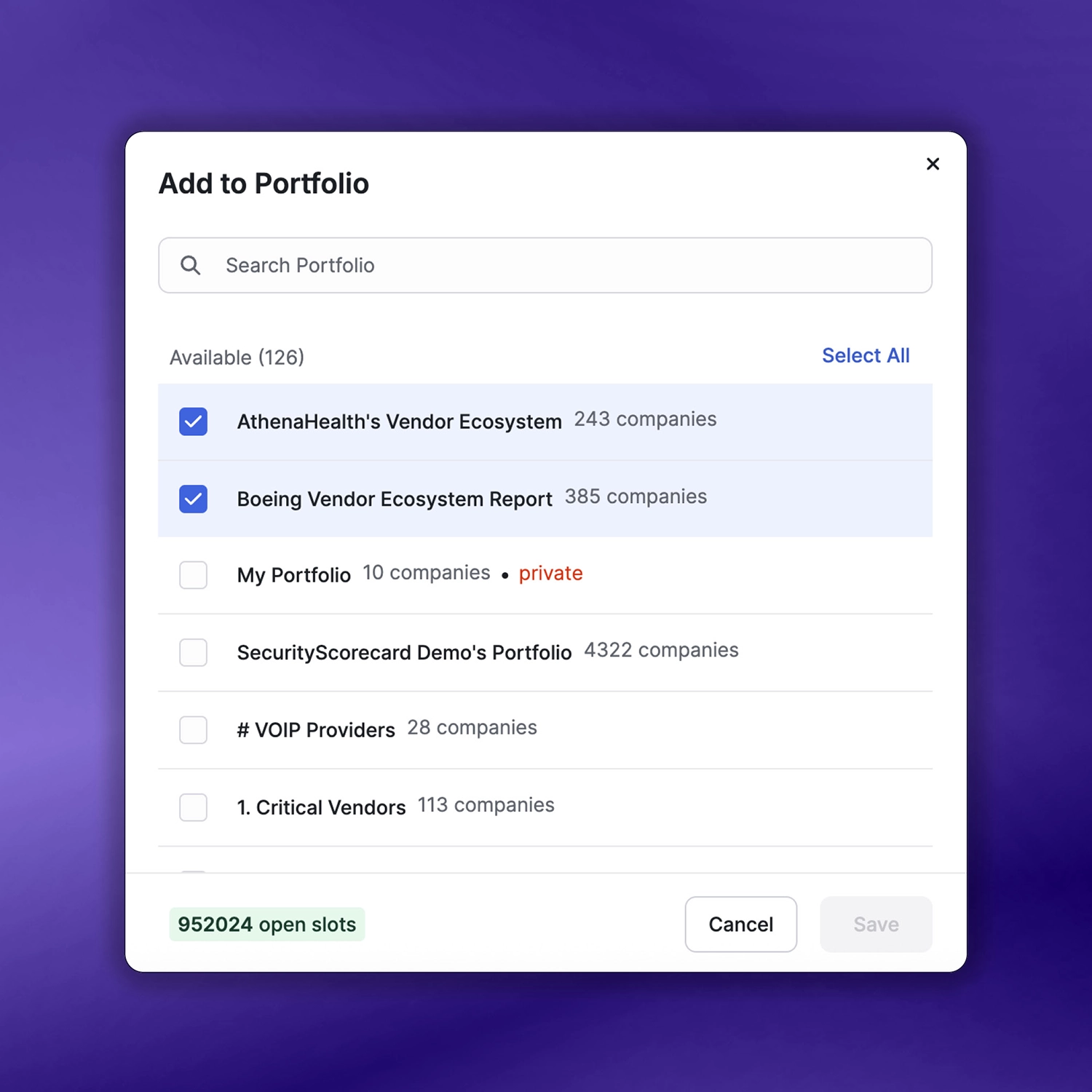
Portfolio Analytics
- Group ratings by business unit, geography, or criticality to identify systemic weaknesses across a diverse global enterprise.
- Automatically categorize vendors into risk tiers based on their ratings to prioritize high-impact remediation efforts effectively.
- Transform portfolio data into high-level risk summaries that communicate ecosystem health to board-level stakeholders instantly.
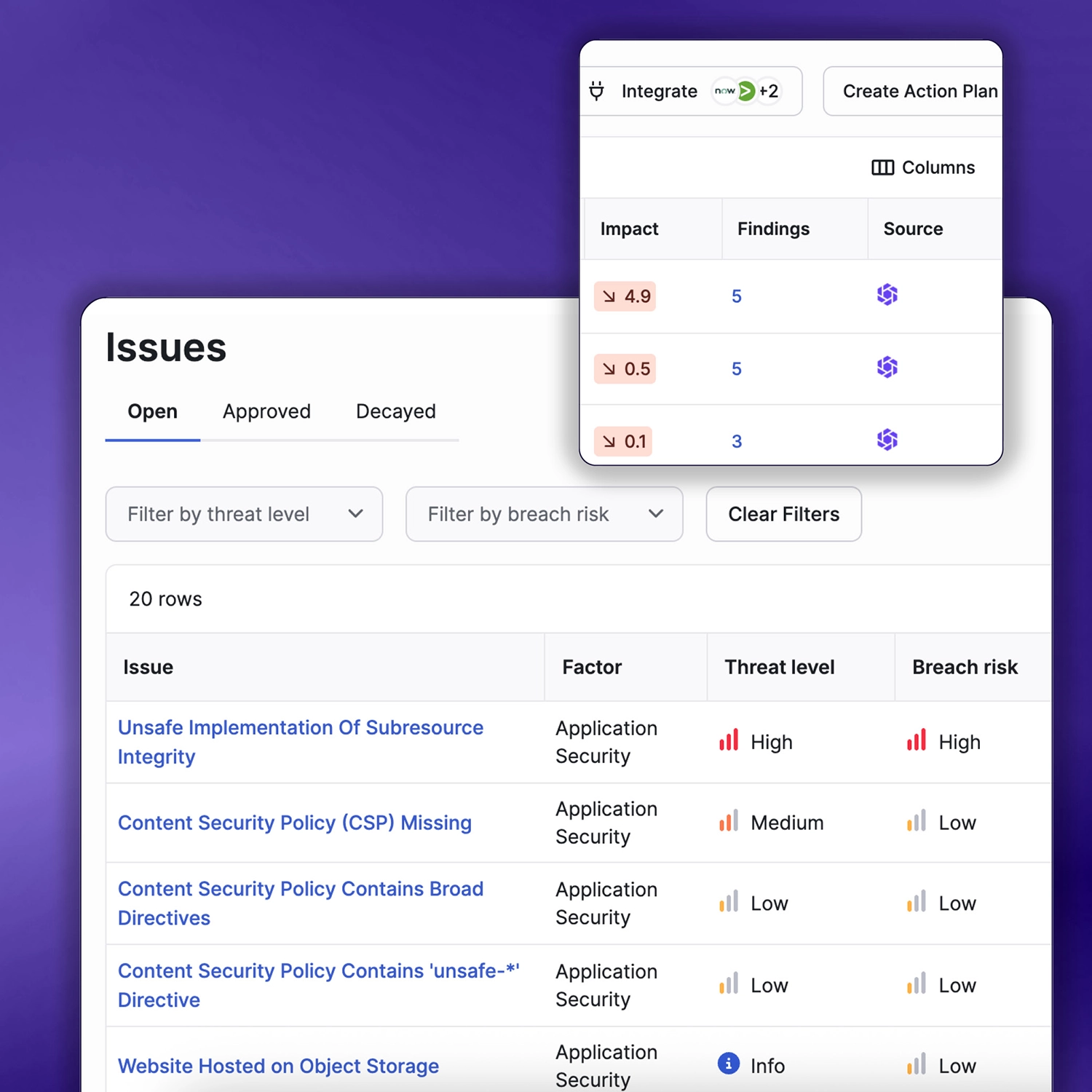
Signal Provenance
- Every score is backed by data—view the specific IP, timestamp, and vulnerability that triggered the rating change
- Access the underlying technical telemetry used to generate scores, ensuring absolute transparency and reducing disputes with third parties
- Maintain a defensible record of all identified security issues and their discovery dates for compliance and regulatory requirements
Outcomes
Assess the security posture of your own organization
Protect your supply chain against cyber risks
Find previously unknown risks in your extended supply chain
Data-Driven Insurance

Intelligence-Driven Features for Proactive Defense
Leverage advanced automation, granular reporting, and patented attribution to transform raw data into a strategic security advantage.
Access timely, relevant information for any organization, including a complete digital footprint, historical rating trends, current security issues, and verified incidents.
Seamlessly group and organize your ecosystem’s scorecards by criticality, geography, or business subsidiary to monitor risk at scale.
Generate board-ready summaries, peer benchmarks, and deep-dive CISO overviews to communicate risk and track issue-type trends over time.
Use event-based triggers to automatically take action, such as notifying a team or generating a report, the moment a score drops or a new breach is detected.
Instantly generate remediation roadmaps from any scorecard to prioritize resources and resolve vulnerabilities that have the most significant impact on your rating.
Automate complex security tasks, analyze entire portfolios simultaneously, and compile information all in one place.
Related resources
Frequently Asked Questions (FAQs)
Everything you need to know about SecurityScorecard’s Security Ratings offering
What are cybersecurity ratings, and how do they help?
Security ratings are objective, external assessments of an organization’s cybersecurity posture, represented by letter grades. They provide a clear and quantifiable view of cyber risk, enabling organizations to identify potential threats and security incidents early.
Why is continuous monitoring important for cybersecurity?
Continuous monitoring is essential for maintaining a resilient security posture. It helps organizations address vulnerability management, reduce risk exposure, and respond swiftly to potential risks.
How does TITAN AI support third-party risk management programs?
Our platform enhances third-party risk management by offering tools for risk assessment and continuous monitoring. This ensures your ecosystem is secure and protected from potential threats and security breaches.
What makes TITAN AI’s ratings unique?
Our security ratings are the best predictor of breach – companies with an “F” rating are 13.8x more likely to experience a breach than companies with an “A” rating. Unlike other security ratings that rely on judgment, SecurityScorecard’s ratings uses an ML/AI-based scoring approach to identify issues predictive of breach and algorithmically determine their impact on breach predictability.
How do security ratings influence informed decisions?
By using security ratings services, organizations can make informed decisions about their third-party risk management program, prioritize vulnerability management, and ensure a resilient security posture across their digital ecosystem.
How do prospective customers benefit from using SecurityScorecard?
Prospective customers can quickly gain insights into their own cybersecurity posture and compare it against industry benchmarks. This helps them identify areas for improvement, build trust with partners, and make informed decisions about addressing cybersecurity risks.