Telecommunications Industry
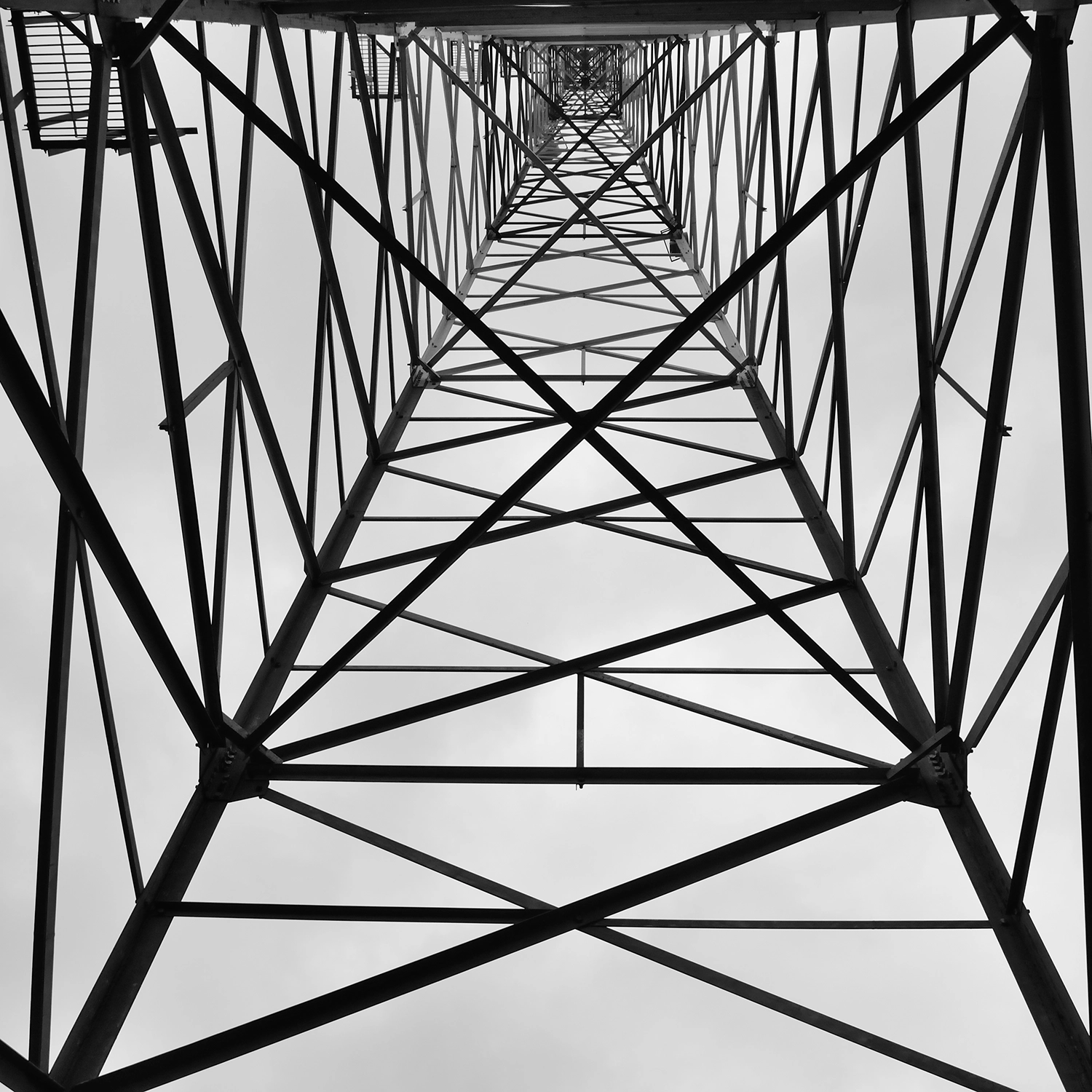
Secure the Backbone of Modern Connectivity with TITAN AI
The Critical Consequences of Telecom Supply Chain Risk
Targets of National Consequence
Telecoms anchor global finance and communications, making them high-value targets for nation-state actors seeking to take down critical infrastructure.
The Invisibility Gap
Static ratings and annual reviews leave vast network surfaces exposed to active threats that emerge between point-in-time security assessments.
Escalating Fourth-Party Exposure
Telecom supply chains face indirect exposures at double the global average, creating hidden attack paths through your vendors’ own suppliers.
The Transition from Reactive to Threat-Informed Defense
SecurityScorecard transforms telecommunications risk programs from reactive compliance hurdles into proactive, threat-informed defenses. By autonomously unifying global threat intelligence with vendor data, TITAN AI identifies and resolves supply chain weaknesses at the source before they can disrupt the backbone of modern connectivity.
This transformation allows your team to move beyond periodic snapshots to catch threats as they emerge across your entire digital and physical ecosystem.
- Scale program coverage 10x. Empower your team to defend a global ecosystem with absolute certainty by replacing fragmented spreadsheets with AI-accelerated workflows.
- Identify zero-day threats in 48 hours. Utilize real-time telemetry directly linked to risk findings for faster, validated remediation across your entire connectivity ecosystem.
- Illuminate fourth-party blind spots. Use persistent discovery to identify hidden risks in your extended network, where breaches can double the global average.
75%
reduction in supply chain breaches reported by organizations using SecurityScorecard.


How Telecom Detects and Responds to Risk
With TITAN AI the telecommunication industry can focus on operational defense at a massive scale.
- TITAN Watch
- TITAN Assess
- TITAN Secure
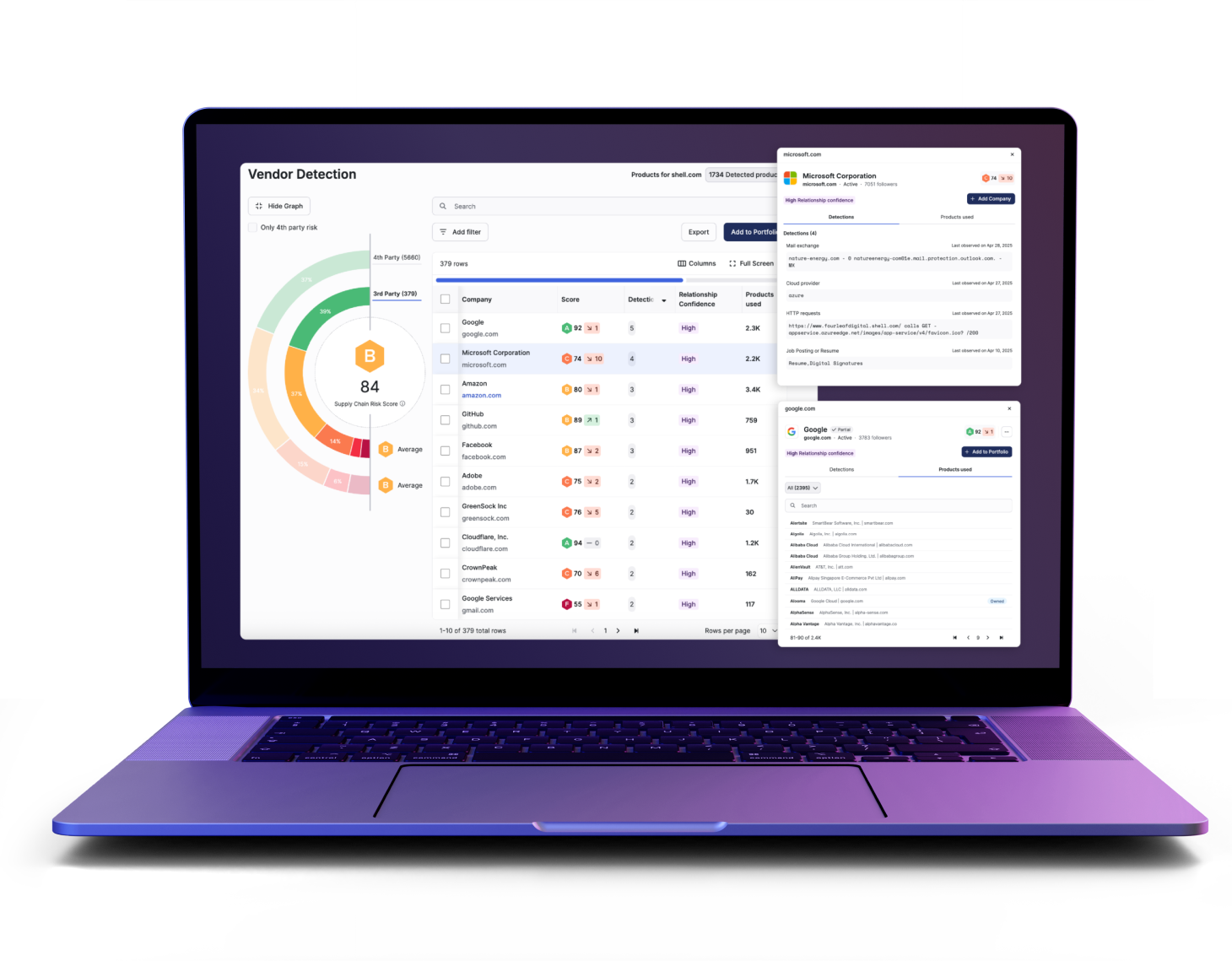
Gain Foundational Visibility into Sprawling Connectivity Networks
- Automatically detect unreported vendors and visualize high-risk connections across your extended digital ecosystem to eliminate third-party blind spots
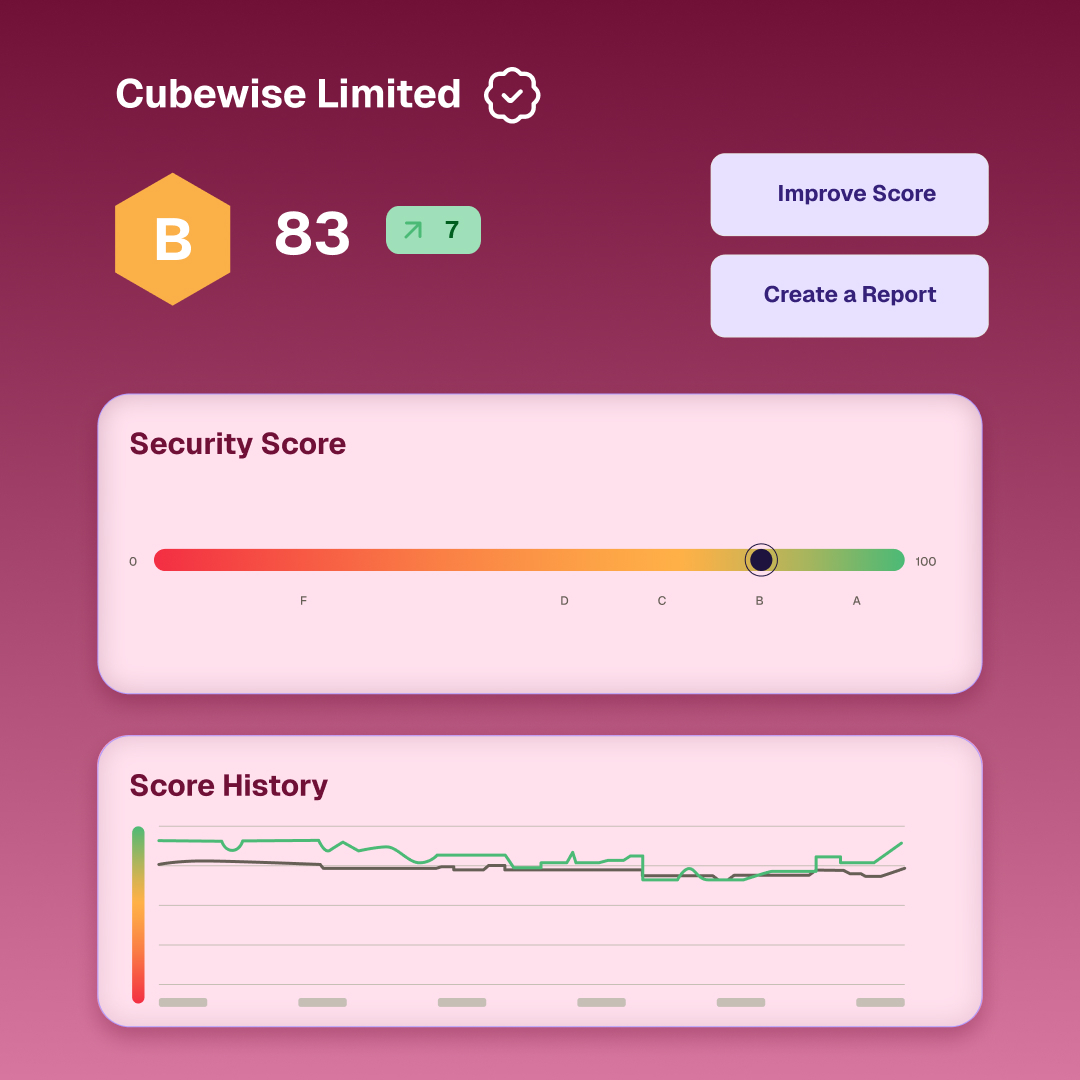
- Monitor security ratings in real-time to understand exactly how specific risk issues impact your overall network hygiene and reliability
- Identify active threats early with continuous outside-in telemetry covering over 12 million organizations in the global supply chain
Automate the Manual Grind to Scale Your Global Risk Program
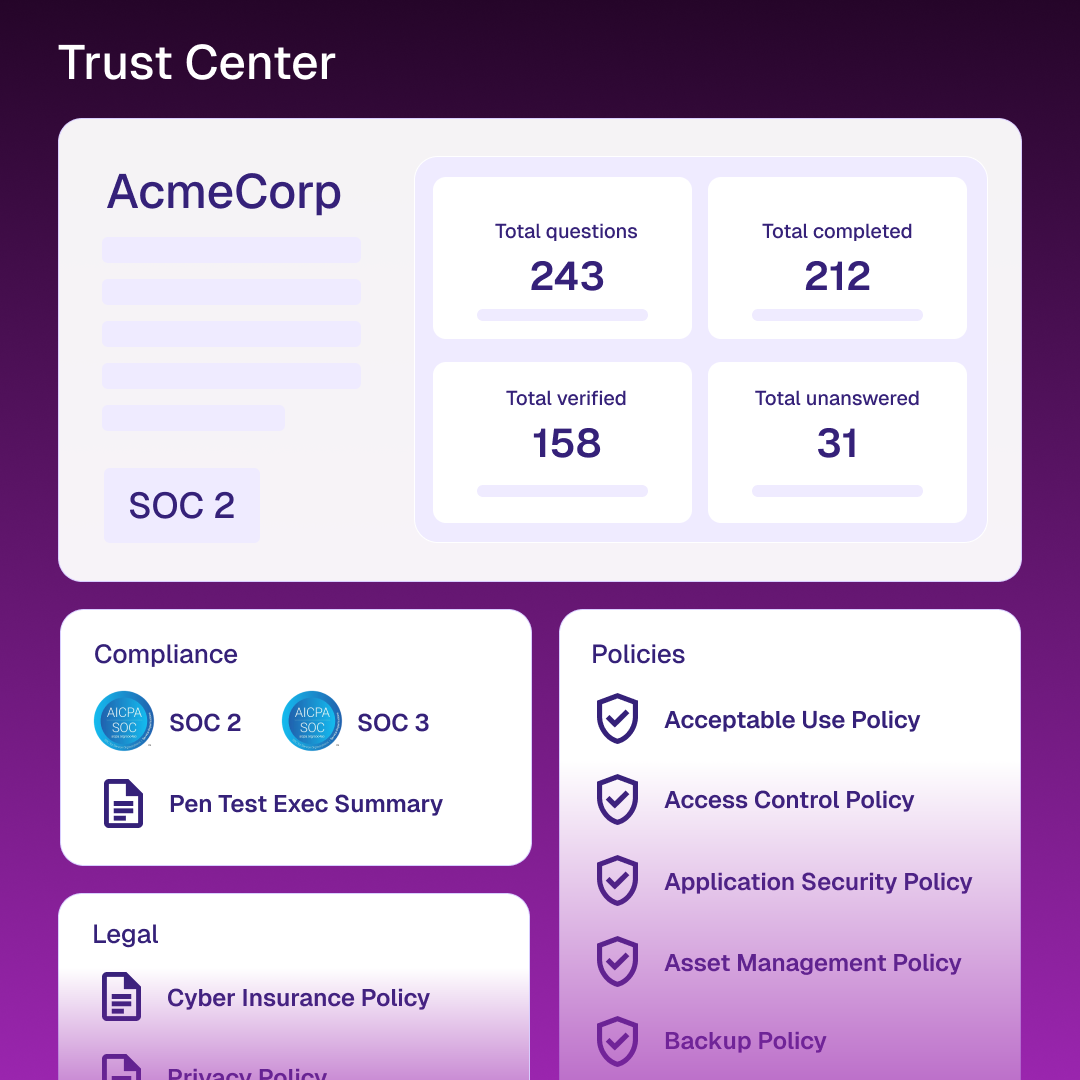
- Speed up assessment cycles by using AI to parse complex vendor documentation and automatically map findings to specific regulatory controls
- Focus on high-value results by reducing manual effort by 95% across your third-party risk management and information gathering workflows
- Build a repeatable risk program that scales to 40,000 vendors to handle the operational complexity of massive telecom ecosystems
Operationalize Threat Response to Prevent Infrastructure Outages
- Coordinate multi-vendor remediation at scale through centralized workflows that turn visibility into immediate, collaborative action across the supply chain
- Prioritize real risk using analysis that correlates supplier weaknesses with critical business context to identify high-probability attack paths
- Neutralize threats at the source quickly to safeguard business continuity and prevent systemic infrastructure disruption in essential connectivity services

Results for Telecom Risk Teams
75% Breach Reduction
9x Higher Vendor Engagement
Demonstrable Grid Control
Attribution Accuracy
Tools Built for Global Connectivity Resilience
Turn complex telemetry into coordinated action with capabilities designed for mature telecom security programs.
Always-on monitoring replaces static reviews, utilizing automatic discovery to uncover unpatched infrastructure and sprawling fourth-party connectivity dependencies across global networks.
Streamline ninety-five percent of manual work via automated questionnaire validation and risk tiering to modernize your massive supplier ecosystem.
Neutralize threats by detecting risks in real-time and using rapid triage to contain incidents before they cause network outages.
Convert technical findings into clear financial impact metrics and quantified supply chain loss to present defensive narratives for leadership.
Use network criticality and connectivity importance to rank technical signals, ensuring your team targets the suppliers introducing meaningful risk.
Provide a dynamic, transparent source of truth for your security controls to securely reduce friction from repetitive partner requests.
Resources for Telecom Security Professionals
Frequently Asked Questions (FAQs)
Find direct answers regarding systemic risk, operational continuity, and supplier oversight in the connectivity sector.
Find answers in our help centerHow does this protect unpatched infrastructure?
TITAN AI monitors for unpatched vulnerabilities and exposed admin interfaces across your entire supply chain to disrupt attacks before they occur.
How fast can we see our network risk score?
You gain instant insight into your attack surface and security rating the moment you set up your account, with data validated against sector norms.
Does this replace our existing SOC tools?
No, TITAN AI is API-first and pushes context directly into your existing SIEM and ticketing tools like Jira or ServiceNow via native connectors.
How do you find vendors we haven’t reported?
We use AI-driven discovery to analyze digital connections and identify vendors in your ecosystem that were previously unknown.
How accurate is the network telemetry?
Our organically collected intelligence provides 99.9% accuracy, ensuring that the risk signals you act upon are validated for high-consequence connectivity decisions.
Can we monitor our fourth-party risk?
Yes, TITAN AI illuminates your entire supply chain to identify risks in your extended fourth-party network, which often bypass primary defenses.