TITAN AI FOR CRITICAL INFRASTRUCTURE
Command the Resilience of Your Essential Service Ecosystem
Solutions
Highly Targeted Assets
Critical infrastructure faces a 47% third-party breach rate, higher than the global average, driven by nation-state and criminal targeting.
Systemic Supply Chain Risk
Reliance on complex ecosystems creates entry points that allow attackers to bypass hardened perimeters via vulnerable third-party weaknesses.
Personnel Constraints
Infrastructure security teams often lack the headcount to manually inspect and respond to every signal across sprawling physical and digital environments.
Beyond “Check-the-Box” Compliance
SecurityScorecard transforms critical infrastructure risk programs from reactive compliance hurdles into proactive, threat-informed operational resilience. By unifying global threat intelligence with vendor data, TITAN AI identifies and resolves supply chain weaknesses at the source before they can disrupt energy grids, transportation networks, or public utilities.
This transformation allows your team to move beyond “check-the-box” snapshots to catch systemic threats as they emerge across your entire ecosystem.
- 95% Less Manual Effort: Automate the assessment workload and eliminate the information-gathering grind that drains infrastructure teams.
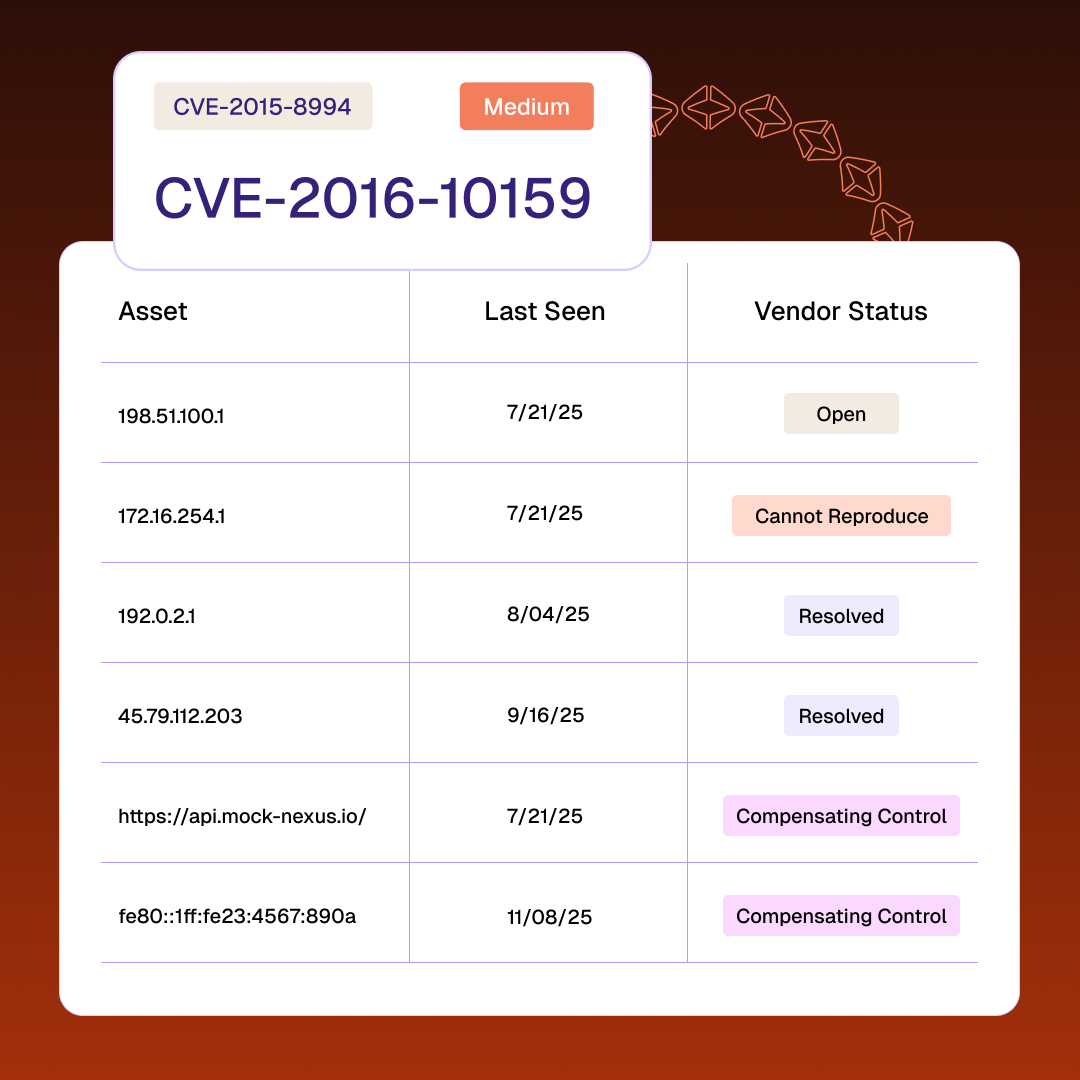
- Eliminate Third-Party Blind Spots: Deploy persistent discovery that illuminates risks in your fourth-party ecosystem and critical supply chain dependencies.
- 48-Hour Zero-Day Response: Identify and remediate critical vendor vulnerabilities in as little as 48 hours to ensure continuous public service operations.
75%
drop in supply chain breaches using SecurityScorecard.


Reducing Systemic Supply Chain Risk for Critical Infrastructure
Deploy an AI-accelerated platform that transforms real-time visibility into coordinated action across your entire supply chain
- TITAN Watch
- TITAN Assess
- TITAN Secure
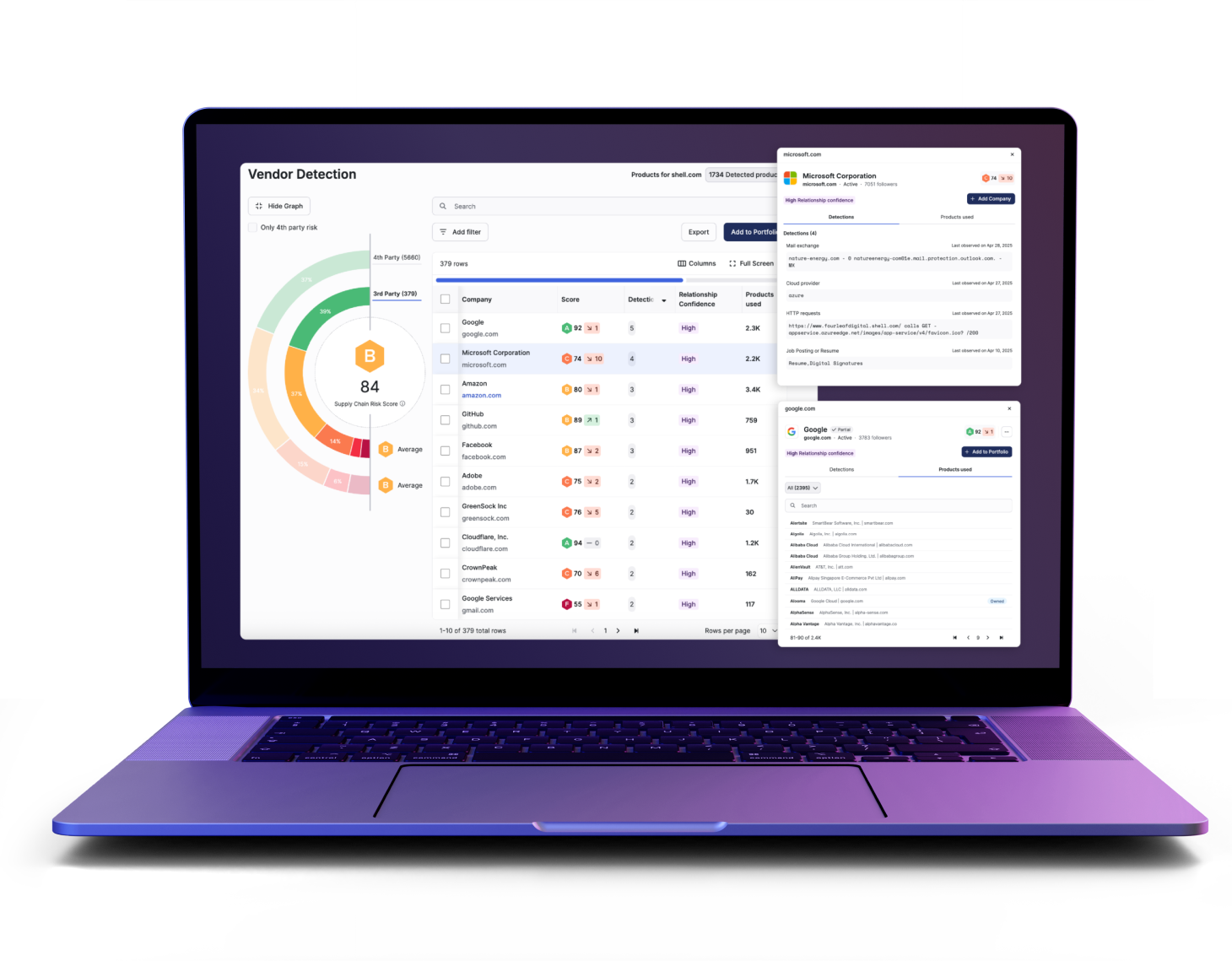
Gain Foundational Visibility into Sprawling Ecosystems
- Automatically detect unreported vendors to eliminate blind spots across your entire digital and physical operational ecosystem
- Monitor security ratings in real-time to understand how specific vendor issues impact your organization’s hygiene and overall risk
- Identify active threats early with continuous outside-in telemetry covering more than 12 million organizations globally
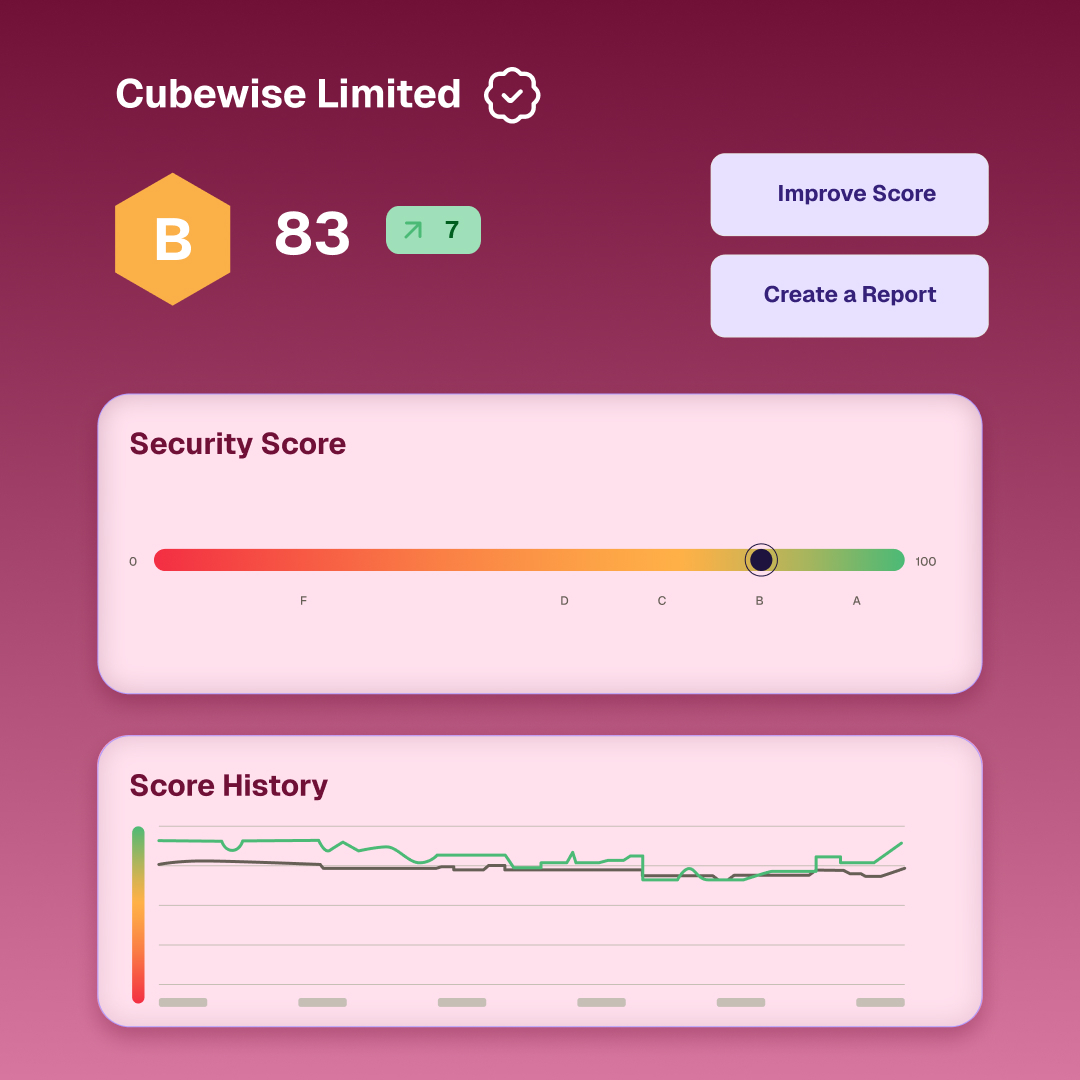
Automate the Manual Grind and Scale Your Program
- Speed up assessment cycles by using AI to parse complex vendor documentation and automatically map findings to security controls
- Focus your team on high-value results by reducing manual effort by 95% across your third-party risk management workflows
- Build a repeatable risk program that scales to 40,000 vendors without increasing your current internal security headcount
Operationalize Threat Response and Incident Containment
- Coordinate multi-vendor remediation at scale through centralized workflows that turn visibility into immediate, collaborative action
- Prioritize the most critical risks by identifying which vendors are most likely to drive the next major incident
- Neutralize threats at the source quickly to safeguard business continuity and prevent outages in essential community services
Results for critical infrastructure teams
48-Hour Zero-Day Response
10x Vendor Coverage Scale
Defensible Regulatory Control

Tools Built for National Resilience
Turn complex telemetry into coordinated action with capabilities designed for mature infrastructure security programs.
Always-on monitoring replaces point-in-time reviews, utilizing automatic discovery to uncover hidden OT assets and sprawling fourth-party supply chain dependencies
Streamline 95% of manual work via automated questionnaire validation and risk tiering to modernize your expansive supplier ecosystem.
Neutralize threats by detecting risks in real-time and using rapid triage to contain incidents before they halt essential services.
Convert technical findings into clear financial impact metrics and quantified supply chain loss to present defensive narratives for leadership.
Use service criticality and public safety importance to rank technical signals, ensuring your team targets the suppliers introducing risk.
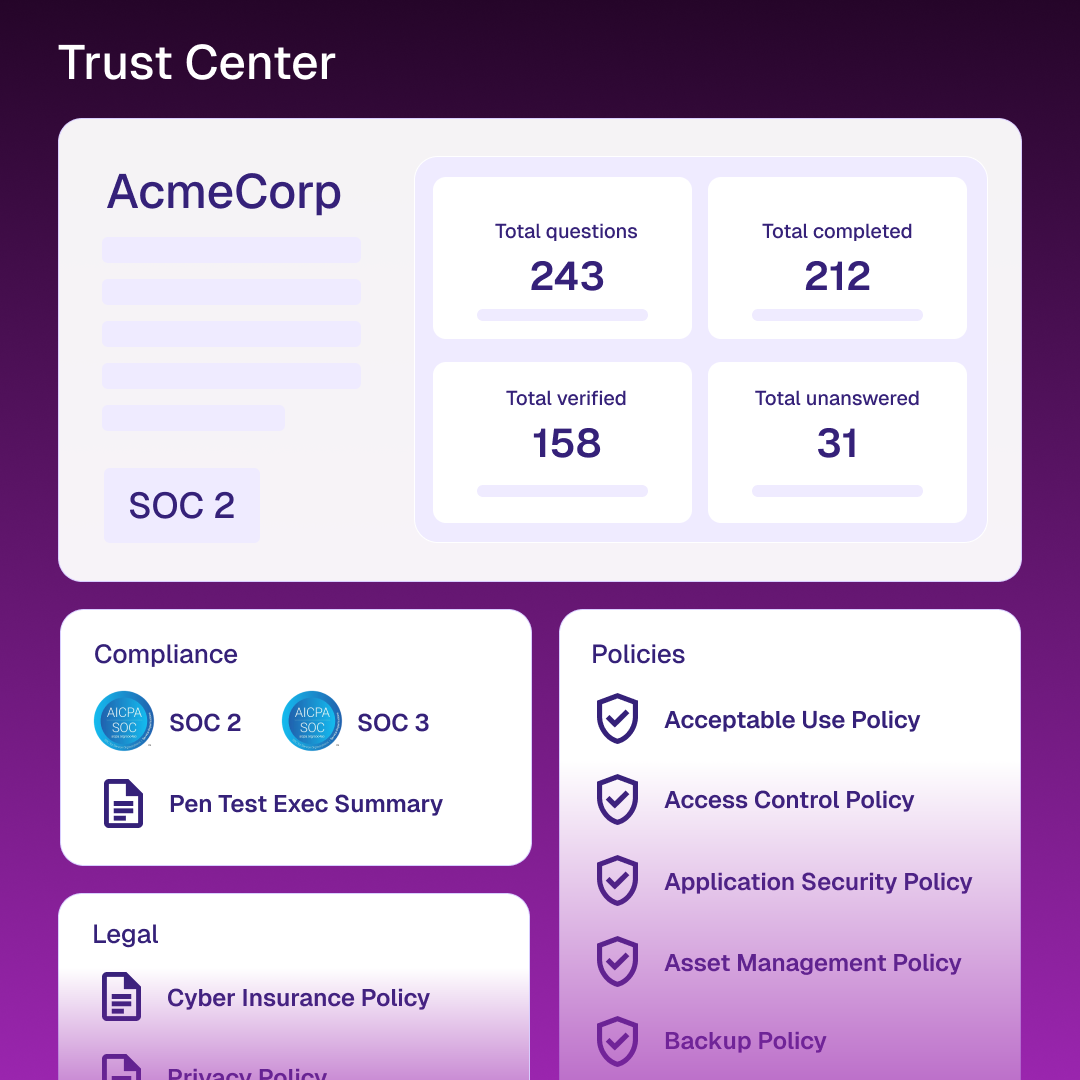
Provide a dynamic, transparent source of truth for your security controls to securely reduce friction from repetitive partner requests.
Related resources
Frequently Asked Questions (FAQs)
Find direct answers regarding systemic risk, operational continuity, and supplier oversight in the public and private sectors.
Find more answers in our help centerHow does this help with regulatory oversight?
SecurityScorecard allows agencies and regulators to take a risk-based approach to oversight, pinpointing weakest links and major threats through patented graded scorecards.
Can we use this for Pipeline or Rail operations?
Yes, the TSA has awarded contracts to enable pipeline and rail operators to assess their cybersecurity posture and remediate observed risks.
What is the FedRAMP status?
SecurityScorecard is designated as FedRAMP and StateRamp Ready, enabling government entities to measure and resolve cyber risk with a certified solution.
How do you find vendors we haven’t reported?
We use AI-driven discovery to analyze digital connections and identify vendors in your ecosystem that were previously unknown.
How accurate is the data?
Our organically collected intelligence provides 99.9% accuracy, validated across over 12 million scored organizations.
Can we monitor our fourth-party risk?
Yes, TITAN AI illuminates your entire supply chain to identify risks in your extended fourth-party network, which often bypass primary defenses.