TITAN AI for Healthcare Systems
Secure Patient Care Across Your Entire Supply Chain
A few of our healthcare partners
Navigating the Healthcare Resilience Gap
High-Value Data Targets
Healthcare records command premium prices on the black market, making your expansive vendor network a primary target for systemic ransomware attacks.
The Invisibility Gap
Static questionnaires leave your organization exposed to active threats that emerge between annual reviews, creating dangerous blind spots in patient safety.
Critical Downtime Risk
Hyperconnected health systems cannot tolerate service disruptions; supply chain breaches directly impact clinical operations and the quality of patient care.
Command Your Healthcare Ecosystem With Certainty
SecurityScorecard transforms healthcare risk programs from reactive compliance hurdles into proactive, threat-informed clinical resilience. By autonomously unifying global threat intelligence with vendor data, TITAN AI identifies and resolves supply chain weaknesses at the source before they can disrupt patient services, medical device networks, or sensitive Electronic Health Record systems.
This transformation allows your team to move beyond point-in-time snapshots to catch systemic threats as they emerge across your entire healthcare ecosystem.
- Automate 95% of the manual grind: Replace manual spreadsheets and questionnaires with AI-accelerated workflows that map findings directly to HIPAA and NIST controls.
- Illuminate fourth-party blind spots: Use persistent discovery to identify risks in your medical device manufacturers and EHR providers.
- Neutralize threats in 48 hours: Use real-time telemetry to identify and remediate zero-day vulnerabilities before they lead to a clinical breach.
75%
decrease in third-party breaches reported by organizations using SecurityScorecard.


Built for Complex Healthcare Supply Chains
Deploy a living source of truth that integrates with your existing GRC and SOC tools to strengthen clinical resilience.
- TITAN Watch
- TITAN Assess
- TITAN Secure
- TITAN MAX Services
- Threat Intelligence
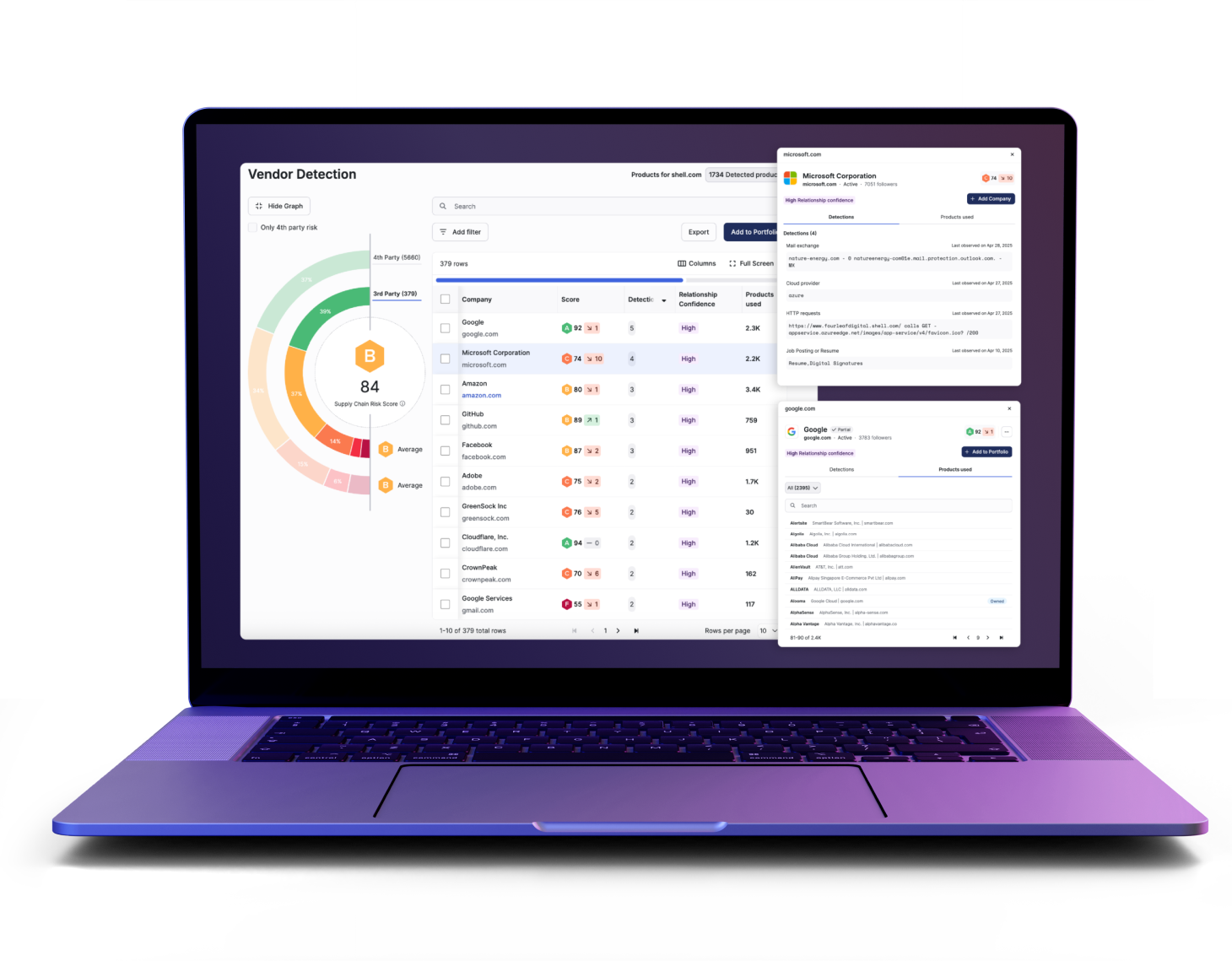
Continuous Visibility Across Your Extended Medical Ecosystem
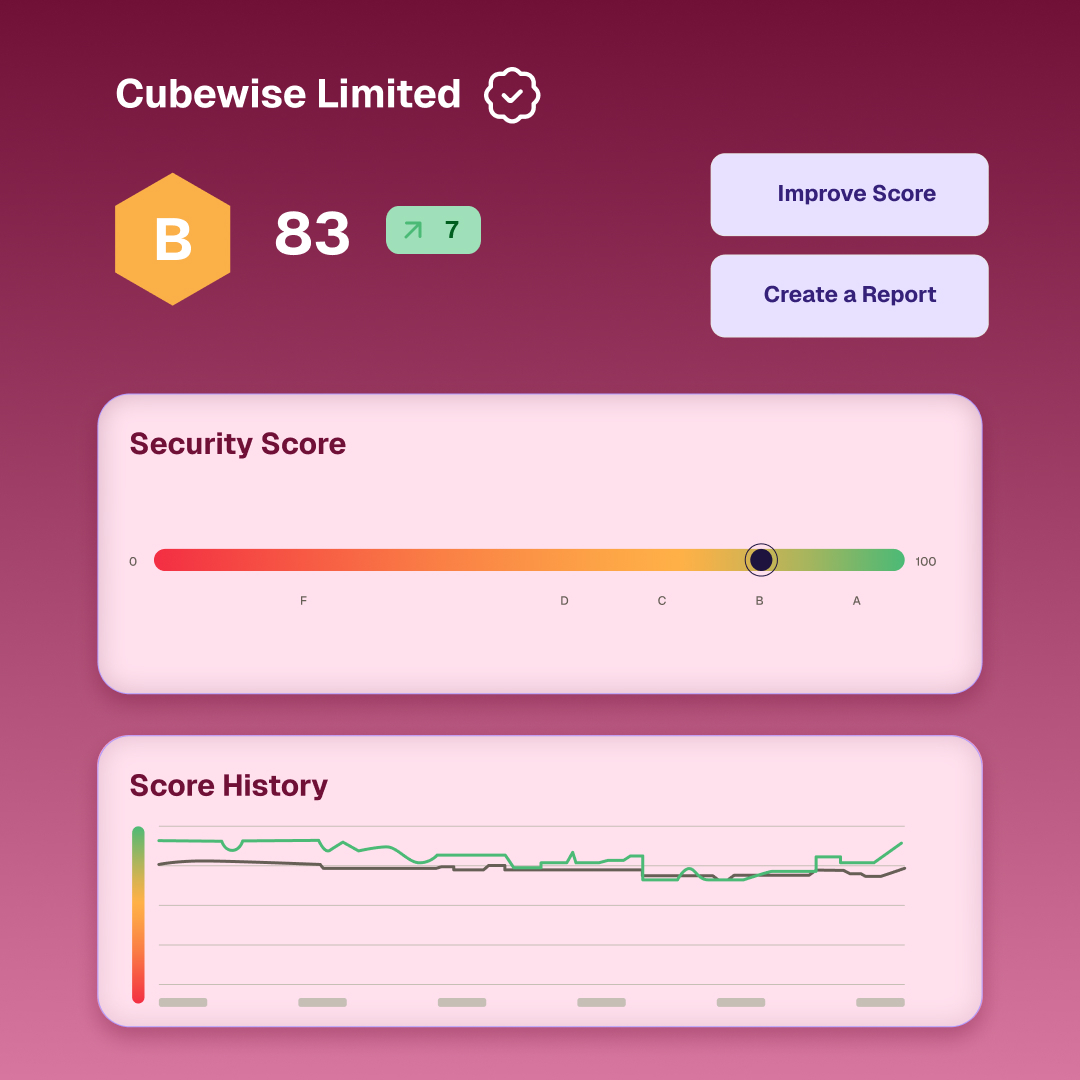
- Monitor security ratings in real-time to understand exactly how specific risk issues impact your HIPAA compliance posture
- Use automatic discovery to visualize high-risk connections across your extended medical supply chain, including previously unreported entities
- Identify emerging threats early with continuous outside-in telemetry that covers both EHR systems and medical device networks
Scale Your Healthcare Risk Program Without Increasing Headcount
- Accelerate audit cycles by utilizing AI to parse vendor documentation and automatically map findings to healthcare regulatory controls
- Focus on high-value mitigation by automating the manual information-gathering processes that typically drain clinical security budgets
- Build a repeatable third-party risk program capable of scaling to 40,000 vendors without adding additional internal staff
Operationalize a Proactive Defense for Clinical Continuity
- Neutralize threats to core business operations immediately to safeguard hospital revenue and ensure continuous patient care
- Coordinate multi-vendor remediation at scale through automated engagement workflows that eliminate the friction of manual follow-ups
- Prioritize critical healthcare threats using predictive analysis that correlates specific supplier weaknesses with their potential clinical impact
Expert Support to Navigate Complex Healthcare Risk
- Advance your program’s maturity using expert-led services without the need to build a dedicated in-house team
- Modernize your assessment lifecycle with AI-augmented validation to significantly reduce the toil associated with manual healthcare audits
- Utilize a Vendor Risk Operations Center to manage continuous monitoring and coordinate supplier responses during critical security incidents

Identify Emerging Threats with Organically Collected Clinical Intelligence
- Trace malicious infrastructure back to its source using internet-wide deep-scan data and historical mapping to protect patients
- Monitor the dark web for botnet traffic and leaked patient credentials to flag compromised accounts before fraud occurs
- Process billions of weekly events to identify zero-day vulnerabilities in your medical tech stack within 48 hours

Measurable Results for Healthcare Leaders
48-Hour Zero-Day Response
Ten Times Vendor Coverage Scale
Faster Remediation
Defensible HIPAA Control

TITAN AI is Built for Complex Healthcare Supply Chains
Turn visibility into measurable outcomes with tools designed for the modern clinical security leader.
Always-on monitoring replaces point-in-time reviews, utilizing automatic discovery to uncover hidden clinical assets and medical device supply chain dependencies.
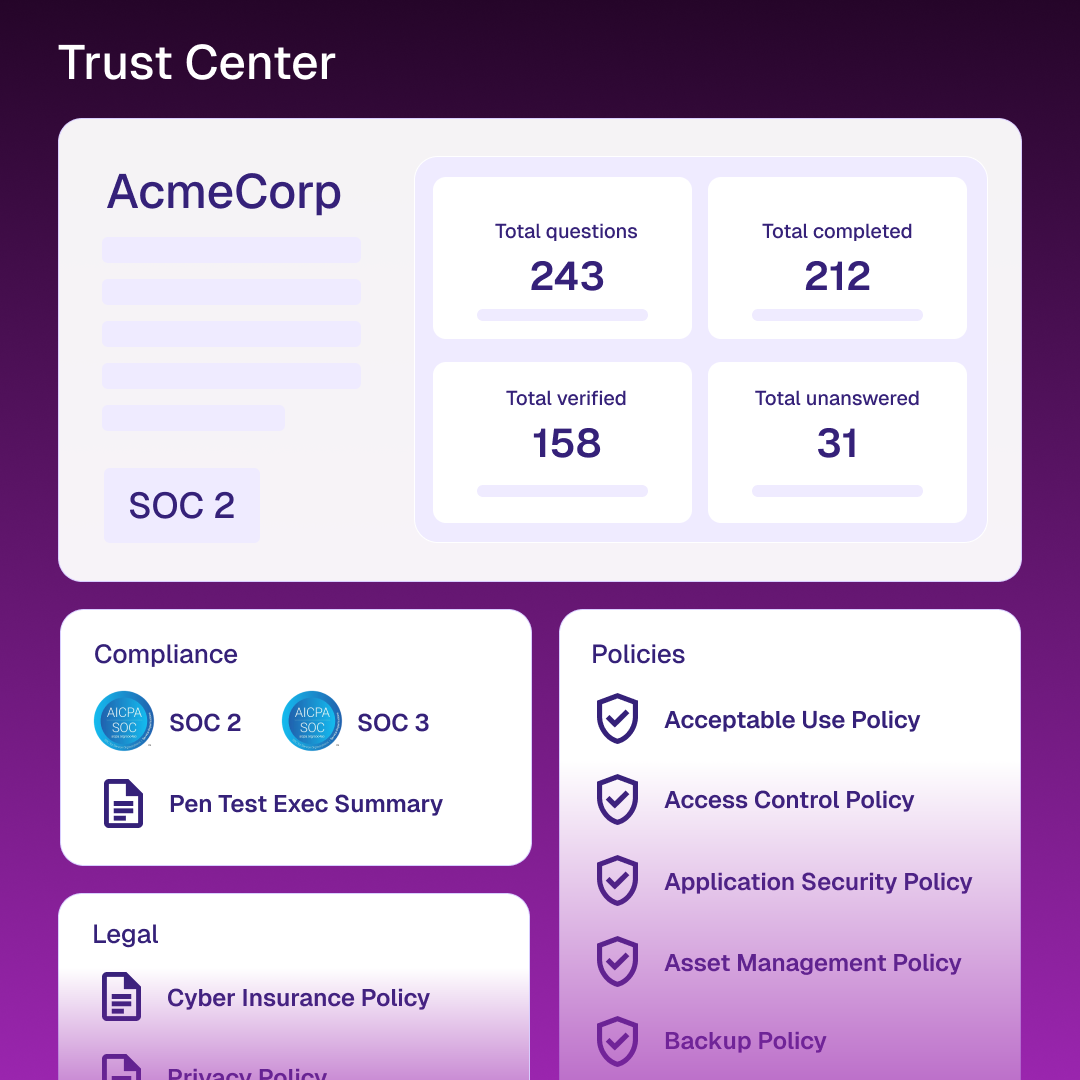
Streamline 95% of manual work via automated questionnaire validation and risk tiering to modernize your traditional audit lifecycle.
Neutralize threats by detecting risks in real-time and using rapid triage to contain incidents before they impact patient services.
Convert technical findings into clear financial impact metrics and quantified supply chain loss to present defensive narratives for leadership.
Use clinical criticality and patient data importance to rank technical signals, ensuring your team targets the vendors introducing risk.
Provide a dynamic, transparent source of truth for your security controls to securely reduce friction from repetitive partner requests.
Related resources
Frequently Asked Questions (FAQs)
Find direct answers here or explore our help center for technical medical device security guides.
Find more answers in our help centerWhy are healthcare systems such prime targets in 2026?
Patient records have high resale value and clinical downtime is intolerable, making ransomware highly profitable for attackers.
How does TITAN AI automate HIPAA compliance?
It unifies findings directly to HIPAA controls and automates the collection of audit evidence from vendor documentation.
How fast can we see our risk score?
You can gain instant insight into your attack surface and security rating the moment you set up your account.
Can we monitor medical device manufacturers?
Yes, the platform identifies threats across vendor networks, including medical device manufacturers and EHR providers.
How do you find vendors we haven’t reported?
We use AI-driven discovery to analyze digital connections and identify vendors in your ecosystem that were previously unknown.
Can we monitor our fourth-party risk?
Yes, TITAN AI illuminates your entire supply chain to identify risks in your extended fourth-party network, which often bypass primary defenses.